Articles about Cryptography - Section 4
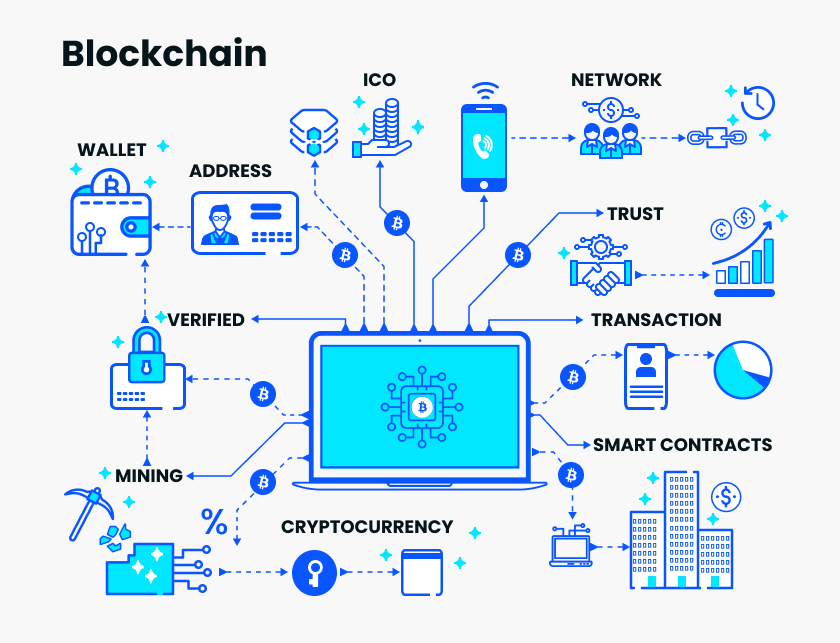
Decoding technology community: Github blockchain code library exceeds 50,000, this is the most concerned
Source: PANews The Ethereum Annual Developers Conference DevCon 5 just came to an end in Osaka, Japan. The conference...
Introduction to Blockchain | Cryptography in Bitcoin: Fundamentals of Digital Signature and Transfer
Let's take a step by step, let's take the easiest email as an example. Now A sends an email to B. This emai...
Ratio Chain Research Institute | A Threshold Signature System under the Hypochronous Network Hypothesis
In recent years, threshold cryptography has gradually been applied in the blockchain system, which is divided into th...
Cryptography in Bitcoin: Five characteristics of hash function and mining principle
Bitcoin is the world's first successful cryptocurrency, and previous attempts have not effectively solved variou...
Introduction to Asymmetric Encryption: Vernacular Analysis of Private Keys, Public Keys, RSA
All previous encryption methods were symmetric encryption, and the straightforward point is that both encryption and ...
Symmetric Cryptography in the Computer Age: From $100 Franklin to Binary XOR to AES
The era when computers did not appear was classical cryptography, and after the advent of computers, modern cryptogra...
Explaining what is a "zero knowledge proof" with Halloween candy may be a very popular explanation of cryptography…
Last week, we illustrated zero-knowledge proofs, explaining what the most common cryptography in the blockchain is, a...
The history of cryptography changes: the enlightenment of the two pits in Germany and the Enigma machine to the mining machine manufacturers
The legend of the Enigma machine is divided into two parts. The first part is his encryption method, and the second p...
What does Google's quantum breakthrough mean for blockchain cryptography?
Over the years, we have been warned that the breakthrough in quantum computing is just around the corner. When this d...
The cryptography of Wanli fifteen years to Xianfeng ten years: Virginia encryption
Today's content is a prelude to cryptography entering modernization. Although there is no encryption algorithm f...

- You may be interested
- Steven Nerayoff Raises Alarms Over SEC’...
- Should the loss of $23 million in crypt...
- Curious baby Musk asked again, Vitalik ...
- $14,000 sold BTC Novogratz regretted &q...
- The price is approaching $7,500, doubli...
- Crypto experts excited about new AI coi...
- Blockchain Weekly: The trading platform...
- Web3 Gaming New Infrastructure: Listeni...
- Solana Emerges as a Fierce Competitor t...
- Information Release + Programmable Disc...
- Countdown to 5 days, 5G chain network (...
- Filecoin tests online, official team an...
- Article estimates Bitcoin halving date ...
- Blockchain game studio Mythical Games c...
- Under the epidemic, how can blockchain ...
Find your business way
Globalization of Business, We can all achieve our own Success.