Talking about safety from the currency and the "stolen"
Talking about safety from the currency and the "stolen"
UOC avanna
One pot
When a security incident occurs, the shabu-shabu is an excellent excuse for hackers. It is very "romantic."
Selling VPN services will always be serious, saying that it will never keep any records;
- EOS REX security series starts from source code and plays REX (1)
- Bitcoin fled the period of the flood season, nearly 90% of the arrogant mining machine, what is the meaning?
- 12 hours after the stolen 7000 bitcoin was stolen
Apple, FB, all promised, will not reveal user privacy;
Cloud service providers, always hammering the promise, the customer's data security, I will protect it… I have no luck.
In any case, seeing the hackers who are not the best are the best "back pots."
2. Who is the hacker?
Kevin Mitnick, known as the "number one computer hacker" in the world, but his technology is not the best, and his ideas are often criticized by some peers.
The Art of Deception is one of his works.
The book elaborates on one point: "If you steal your information or banknotes, it is a hacker. Then, the scope of "hackers" includes the trustee you trust."
Misunderstanding 1: Hacker without your password
Many people think that the encrypted data is safe before it reveals the password.
In fact, this is not true.
In a battle between the red and the blue, the Red side has two legions, and the Blue side has only one legion.
However, the Blue side does not require the red-encrypted communication password, but it can use the base station to forge the communication identity of the two Red Army and provide communication services for the Red Army.
Then, winning or losing is easy to predict.
Four. Think more
Do you think "Apple" has the ability to fake a love mad ID?
Do you think the "telegram" has the ability to fake a TG account?
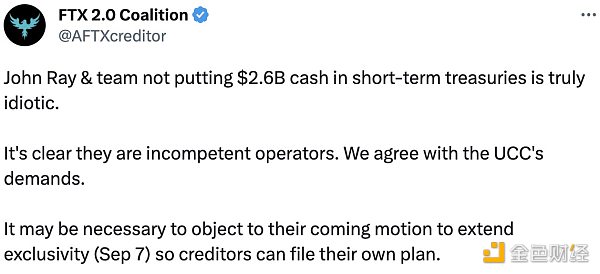
Do you think MT.Gox has the ability to fake a non-existent hacker?
Of course, big companies such as Apple, Telegraph and MT.Gox will never falsify user identities, and they will not create hackers. It will be unethical to infringe on the interests of users.
Although, this malicious act is very difficult to be investigated and evidenced.
V. Self-defense weapons
However, if large enterprises are unable to provide protection for user information data for some reason.
So where do users go from here?
Only pick up the weapons of mathematics.
What is Snowden using?
It is recommended to learn about the technical implementation of Bitmessage or Safeemail.
The former is used by Snowden to convey confidential information and is called "the safest communication tool in the world" by the US Department of Defense.
The latter is based on the new network underlying communication protocol SDTP, and is called "the best and safest communication tool in the world" by the technology executives of the world's largest firewall company.
Both are decentralized, and no one can control the communication pipeline;
Both are based on an identity system rather than an account password system.
This is a very core foundation. Identity cannot be forged by the rights center (that is, it cannot be impersonated), nor can it be denied service by the rights center (that is, the account cannot be deleted).
Only when this core foundation is established, it makes sense to talk about data encryption.
Two grandchildren, no matter how big they are, are not the Buddha (center) who says that it is true and which is true, so it cannot be forged.
7. Misunderstanding 2: Open source and full open source
Both Bitmessage and Safeemail are completely open source on github.
The reason for using the word "complete open source" is also very helpless.
The telegram, also known as open source, but its control center procedures and code is not open source, retaining its right to delete accounts and forgery.
Misunderstanding 3: Point-to-point is very safe
In addition, not all "peer-to-peer" means safe. It is very dangerous for those who help the matchmaking.
Note: Bitmessage and Safeemail are not peer-to-peer, they are discrete.
9. Your last protector
Technology is always confusing, keep in mind: "All the people who pat the chest, say your message, I will help you to ensure safety," you must keep one more eye.
The last thing you can believe is the mathematical mechanism of uncontrolled people.
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Secret Dark Bitcoin Anti-Tracking Tool
- Analysis of the market: Up-and-coming 6000 seccoin money stolen 7000btc, how to develop the market outlook?
- Leading Bitcoin in one step! Bitcoin Cash (BCH) will be hard forked next week to welcome Schnorr signature
- May 8th analysis: amazing and consistent hacking market
- Monthly market report | market value and transaction volume have increased sharply, but only 30% of profitable people
- The currency was stolen again, and the loss was nearly 300 million. How does the exchange protect the security of user assets?
- Analysis of the loss of 7000 bitcoin and the theft of the coin hot wallet