Is the anti-ASIC algorithm beneficial to the security of the PoW?
Coinbase recently changed four different asset recognition requirements, including reducing the block confirmation for Bitcoin from six to three. This article focuses on the perception of PoW security, and it is these views that motivate us to make changes.
Introduction to PoW
All cryptocurrencies define the ownership status within the currency network. In order for cryptocurrency to be available, there must be a way to update the ownership status. In most existing cryptocurrencies, the ownership status is defined by the canonical history of all transactions that have occurred, and they are stored in network nodes in a data structure called a blockchain.
In order to update the status of ownership, there must be a way to add the most recent transaction to the transaction history stored on the blockchain.
- What is the actual trading volume of Bitcoin?
- Babbitt column | Xiao Wei: The formal blockchain project, where is the legal boundary?
- EdenChain and NodeNum jointly released 12 dApp games, one-step login to experience
Different cryptocurrencies add transactions to their blockchain in different ways. In the cryptocurrency of PoW, the blockchain is expanded by the process of mining. The miner packs the newly declared transaction into a data structure called a block and then adds it to the blockchain.
The miners tried to add blocks by resolving the PoW puzzles that were unique to the proposed block. If the miner can find a solution to the puzzle, the miner will declare the block and the resulting solution to the rest of the network.
The rest of the network identifies valid PoW solutions and treats the proposed block as the most recent block added to the blockchain. Please note that the miners' production blocks are not required to be licensed, a fact that allows miners to join or leave the network at will.
In order to determine a canonical transaction history in the event that a miner may generate multiple valid transaction histories (ie, in the presence of different valid blocks or even chains with valid blocks), PoW cryptocurrency accumulates the most workload The blockchain defines the trading history of the specification. (Blue Fox Note: This is the longest chain rule in the Nakamoto consensus.)
The consensus rule introduces the basic attributes of the workload to prove the cryptocurrency: any participant who can find more solutions to the workload than the rest of the network can unilaterally produce a valid transaction history, and the rest of the network will receive it as Standardized trading history. Please note: this does not mean that this participant has unlimited power on the network.
This paper proposes two ideas for the security of PoW cryptocurrency.
Proposition 1: The main utility of mining hardware is the safety features of specific coin mining operations.
If the main utility of the hardware loses value, the hardware owner loses its investment value.
Hardware owners have an incentive to consider the long-term success of the main effects of their hardware. The longer the life cycle of their devices, the more they will invest in the long-term success of the main hardware utilities. At the time of writing, Bitcoin's ASIC mining machine began to have a longer effective life cycle because the efficiency of the new mining machine was decreasing.
This idea is related to the Dedicated Cost Principle.
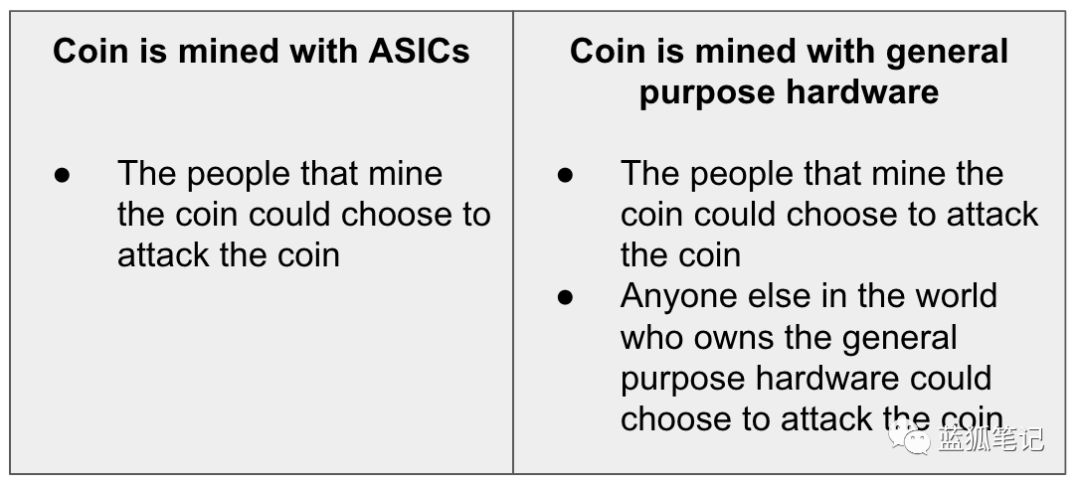
A large pool of computing power outside the token, posing a security threat to the token
What kind of token has the biggest risk of 51% attack? It is those who have a large number of external hashing powers that are not actively involved in the mining of the tokens, which may open mining and destroy the blockchain of the token.
Considering the motivation of hardware owners for their hardware, it is especially important to consider this – if the hardware owners have other utilities besides mining, from which they can profit from their hardware investments, then destroy The negative consequences of a token blockchain are minimal. (Blue Fox Note: The author of this article means that if a piece of hardware is not dedicated to a certain currency mining, and the hardware calculations have a large part of the power and do not participate in the current mining activities, then all of the hardware In order to make a profit, it is possible to launch 51% of attacks. After the attack, the hardware has other uses and is not worried about abolishing it.
Turning the algorithm to "enclosure ASICs" simply allows the world's vast common computing resources to mine, which has the potential to arbitrarily destroy tokens. Therefore, tokens that have implemented "anti-ASIC" algorithms are vulnerable to 51% attacks. (Blue Fox Note: The original intention of anti-ASIC is to let more people participate and prevent the monopoly of the mining machine. What is the logical contradiction here? What are the dilemmas here? Welcome to discuss)
A striking example is that "anti-ASIC" tokens, including BTG, VTC, and XVG, were all attacked by 51%. To date, tokens that have not dominated their hardware category have suffered a 51% double-flower attack. (Blue Fox notes: The meaning of this article is that the tokens with ASIC-specific mining machines have not suffered 51% of attacks)
Case Study: 51% Attack on BTG
In May 2018, the BTG was repeatedly attacked by 51%, resulting in a multi-million dollar double spending. After the attack, BTG developers announced that they would change their PoW algorithm to Equihash-BTG:
“Because Equihash-BTG is different from the existing conventional Equihash pool, we will effectively be in a separate pool of power. This means that BTG will dominate its hash rate on this new PoW algorithm. The algorithm is “personalized” for BTG, which adds an incompatible layer to other tokens, and other tokens are moved to the <144,5> parameter set, such as BTCZ. (We have worked with many other token teams. cooperation.)"
This is a very interesting statement. BTG developers acknowledge the importance of leading hash rates, but they have erroneously concluded that it is important to control the hash algorithm, not the hardware that produces the hash rate.
Unless the hardware that produces the hash rate is dominated by mining, nothing about the hash rate is "personalized" to the BTG. Miners with general hardware that can dig other tokens can change their mining algorithms at will, allowing the hardware to dig BTG tokens without additional investment.
Summary of claim one
The only way that PoW tokens can substantially reduce the risk of attack by 51% is to become the primary utility of mining hardware. A token that can be mined with widely available general-purpose hardware, such as tokens that can be mined with CPU and GPU, lacks this primary security feature.
Proposition 2: ASIC-friendly algorithms will increase manufacturing and ownership diversity
No algorithm can resist ASIC forever, and it's just anti-ASIC.
For any particular computing problem, hardware dedicated to solving the problem is always more efficient than general purpose hardware. In addition to the advantages of writing application-level logic directly to the circuit, dedicated hardware does not have to withstand other hardware-specific requirements such as security isolation, clock interruption, context switching, and other tasks required to support multiple applications. Therefore, no PoW algorithm is always proof against ASIC and is only anti-ASIC.
Empirically, anti-ASIC algorithms have failed to prevent the development of ASICs. Prominent examples include scrypt (LTC), equihash (ZEC, BTG), ethhash (ETH), and cryptonite (XMR).
Anti-ASIC algorithms increase the barrier to entry into the mining hardware market
Anti-ASIC algorithms make it more difficult to build efficient ASIC miners, which is very effective. The result is that chip makers need to invest more and more expertise before they can make an effective ASIC.
Therefore, anti-ASIC only increases the threshold for entering the ASIC market. The result is a greater degree of centralization in the field of mining hardware production, which is what anti-ASIC algorithms are trying to avoid.
Instead, the goal should be to choose an algorithm that makes ASIC mining cheap and easy. This will result in the ASIC being a commodity and will not create significant expertise or IP (IP) thresholds for ASIC manufacturing.
This will lead to a diversification of manufacturers, which will make it easier to encourage the diversity of owners and operators, which is more likely to lead to decentralized mining networks. When developers choose anti-ASIC algorithms, they provide chip manufacturers with a competitive moat, because these chip manufacturers will eventually develop ASIC mining machines based on this algorithm. (Blue Fox Note: The logic of this article is that only ASIC-friendly algorithms can get ordinary mining machine manufacturers to participate, so that more people have goods, and anti-ASIC will only increase the threshold, resulting in stronger, not strong Conducive to decentralized network)
Case study: Monroe currency regular adjustment algorithm
The Monroe R&D team implicitly acknowledges the fact that in the previous strategy of pursuing general hardware mining, the algorithm could not be just anti-ASIC. They seem to realize that trying to permanently prevent ASIC development by developing a killer-level anti-ASIC algorithm seems to be ineffective.
Instead, the strategy they identified was to periodically adjust their PoW algorithm every six months to suppress the incentive to produce dedicated hardware by quickly getting it outdated.
This strategy underestimates the ability of talented hardware designers to quickly integrate functionality into chip design. No matter what mode is integrated, very skilled chip designers can master the development process, and they will inevitably develop a mining machine that meets these PoW changes.
This may force a small group of highly protected developers to try to play a high-risk, high-confidence cat and mouse game, they need to hide their algorithm plans, and there is a huge economy for any member of the team. The temptation prompted him to violate the trust of this small circle and disclose his information to the chip maker.
For the world currency that is not required to be licensed, the key to the decision of the group and the extreme trust of them are not a good feature, and it can be said that the centralization risk it creates is more serious than the risk of miner centralization.
The limitations of this strategy are already clear, and at least three different versions of the mining algorithm ASIC mining machine were successfully predicted and deployed on the XMR network.
Ambition is only important within the scope of achievable
Most arguments that support anti-ASIC are ambitious. The overall goal is usually this: "Make sure the network is not controlled by a few people." This is a great goal. This is critical to ensuring that digital currencies deliver on their promises.
In fact, when the actions taken because of these intentions do more harm than good, all goodwill in the world is completely irrelevant. Ironically, the implementation of anti-ASIC mining algorithms for tokens ultimately led to a greater degree of miner concentration and control.
Summary of claim two
The only achievement of anti-ASIC algorithms is the increased cost and expertise required to create efficient ASICs. This, in turn, means that any significant value PoW tokens will eventually be mined by ASIC mining machines, which will result in highly centralized mining, as successful ASIC manufacturers will have a deep competitive advantage.
in conclusion
Cryptographic currency does not provide a completely equal system, it does not eliminate the advantages of all power structures or additional resources. Compared to opaque, manual, error-prone and licensed existing financial systems, cryptocurrencies have indeed made tremendous progress.
When trying to change the world, it is important to zealously defend your principles. But, equally important, don't let the illusory perfect system become the enemy of a good system.
As digital assets mature, participants must ask themselves whether the industry is running safely by amateurs running old laptops at home, or like almost all other ongoing efforts in human history. The size of the personal interest-driven group invests a lot of resources to promote. Each large-scale professional industry will use specialized equipment, and it is naive to think that cryptocurrency mining will be different or should have different ideas.
——
Listening to it, Blue Fox notes hope to be closer to the truth of the matter through different voices. The following is Monroe's different opinions on this article. Because this article mentions the previous PoW strategy of Monroe. Monroe responded to this article as follows:
On November 8, 2019, Coinbase published an article by Mark Nesbitt about its views on PoW. The article has a good explanation of PoW and puts forward some convincing arguments about the benefits of using ASIC. But it also raises some incorrect opinions and draws a controversial and inappropriate conclusion.
The response in this paper corrects the error and advocates supporting the anti-ASIC route adopted by Monroe developers. Corrections include pointing out that Monroe's efforts to prevent the use of ASICs described in this article are outdated and outdated, as well as technical and philosophical rebuttals about the benefits of ASIC.
problem
In that article, there is a case study of Monroe that focuses on a six-month hard-fork cycle, each of which changes Monroe's PoW algorithm to prevent ASIC utility. Its criticism of cyclical risks and negative impacts is correct and insightful.
However, the cycle is historical, not current, as it was changed in March last year. These issues were resolved with the release of Monroe Software v0.15.0.0 (called Carbon Chamaeleon). After this release, starting from the end of November, a new PoW algorithm called RandomX will be adopted.
By creating random programs, RandomX makes everyday computer CPUs competitive in PoW computing. It is expected that RandomX will be able to achieve ASIC resistance for many years without the need for hard bifurcation, contrary to the scenario mentioned in the case study.
The core of the article is to encourage the use of ASIC's PoW algorithm to better serve cryptocurrencies. It mentions the benefits of anti-ASIC, which is to "ensure that the network is not controlled by a few people", but then it believes that doing so does more harm than good.
In fact, it is critical to prevent hardware manufacturers from maliciously controlling the network. Historically, the controls advocated by ASIC manufacturers have had an adverse effect on cryptocurrencies. For example, it led to the infighting of Bitcoin. Controlled by a small number of people who manufacture hardware can damage Monroe's decentralized model and pose a huge risk.
Keeping the benefits of being independent of the hardware manufacturer is higher than maintaining it, which is a prerequisite for Monroe PoW.
In addition to avoiding power integration, there are many other benefits to running on a commercial CPU. Almost everyone has commercial hardware that gives small miners the opportunity to participate in economic activities and has reason to remain interested and use Monroe.
The CPU's PoW opens up new possibilities for Monroe, including the ability to earn revenue from sleep and intermittent everyday computers. It gives way to people around the world who find themselves abandoned by traditional exchanges to get Monroe. Moreover, it adds concealed benefits to the newly created Monroe, where individual mining can be spent directly without having to go through the exchange.
The article argues that a simple PoW algorithm will lead to the competitiveness of commercial ASICs, as well as the reality of ASIC design and manufacturing, because of its inherent complexity and economies of scale. Even for a hypothetical PoW algorithm with only one construction method, large manufacturers will still manage small challengers through economies of scale. (Blue Fox Note: The above mentioned complex anti-ASIC PoW algorithm brings the threshold of mining machine manufacturing, and the author of this article believes that even if the PoW algorithm is very simple, there will still be economies of scale, large hardware manufacturers still There will be advantages, which is not conducive to decentralization)
Even the hash algorithm SHA-256 is not fully developed. After 18 years of development, researchers are still releasing new optimization techniques for it. ASIC energy efficiency has grown exponentially in recent years, and ASIC's PoW dominates no simple and equal model.
The above ironically suggests: "Whether this industry will be secured by amateurs who run with old laptops at home." This is misleading. Encrypted currency mining is the process of implementing the PoW algorithm to ensure transaction security. It follows the power law, and a small number of miners have most of the computing power.
The choice of various PoW algorithms will exist in professional mines. Anti-ASICs ensure that amateurs are still able to participate in mining, which helps to strengthen the power and decentralization of the network.
As the founder of Symas Corp. and CTO Howard Chu said about RandomX: "The goal is to use hardware that is already ubiquitous, so participation is not a problem, just like Bitmain."
General purpose CPUs such as desktops, laptops, and smartphones are the most common and easily accessible computing devices. Howard has been one of the most active people involved in the development and introduction of Monroe's new RandomX PoW algorithm.
In addition, Monroe is driven by grassroots open source development and ideology. It supports decentralization, capital allocation, and privacy and security innovations, which are difficult to find in large organizations. Distributed and equal PoW mining drives this spirit.
Monroe's vitality
The field of encryption was in the early days, and Monroe was very early. Any debate about technological change must consider the evolutionary nature of cryptocurrencies and consider the fact that decisions will not last forever. The Monroe developers have been formally discussed and can be seen in the public log, which mentions possible future development paths after RandomX.
These include the use of SHA-3 (or similar), a PoW hashing algorithm that can be easily run on an ASIC. The choice of using RandomX in the next few years will take advantage of this flexibility. The Monroe community has a proven track record of integrating new technologies, observations, and developments and can expect to continue doing so in the future, and will continue to leverage the knowledge gained from ASICs and anti-ASICs.
RandomX was developed transparently in the public Github repository and subsequently reviewed by four independent audit teams to demonstrate its potential as a secure and innovative PoW algorithm. We will soon see its effectiveness in maintaining Monroe's network security and decentralization.
to sum up
This article provides a good overview of PoW and has several useful perspectives on the use of ASICs, which is worth considering. However, its expression of Monroe is outdated and some arguments and opinions are flawed.
In a new technology and uncertainty environment, the Monroe community takes a proactive approach to protecting its network from the control of hardware manufacturers. By using RandomX, Monroe stands out for its unique innovation and initiative and brings it to a bright future.
(Link to Monroe's response: https://www.monerooutreach.org/stories/response-to-coinbase.php)
Risk Warning: All articles in Blue Fox Notes can not be used as investment suggestions or recommendations. Investment is risky. Investment should consider individual risk tolerance. It is recommended to conduct in-depth inspections of the project and carefully make your own investment decisions.
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Federal Reserve's latest Financial Stability Report: Stabilizing coins may become a new trading medium
- Ethereum is expected to upgrade to Istanbul on December 7th
- The cryptocurrency wallet GateHub data was leaked and 1.4 million account information was stolen
- Li Lihui, former president of Bank of China: The blockchain needs to be scaled up, and it is urgent to break through five technical bottlenecks.
- Featured | Read the Ethereum community new favorite MarketingDAO
- Yao Yudong, former director of the Central Bank's Financial Research Institute: Called the Dawan District to try the digital currency first
- Grayscale Bitcoin Trust Fund submits registration application to SEC, investors may benefit






