Ace vs. Ace: Against double-flower attacks, who is better with DCR and Bitcoin?
For now, Decred's ability to resist double-flower attacks is not as good as Bitcoin. An effective double-strike attack on the Bitcoin blockchain will cost at least $1.6 billion in new hardware to succeed. The effective double-flower attack on Decred cost only $152.7 million in hardware and ballot (PoS) costs. Therefore, the cost of performing a Decred double-flower attack is only 9.5% of Bitcoin. For a currency whose current market value is only 0.23% of the market value of Bitcoin, it is not bad.
Compare the resistance of Decred and Bitcoin double flower attacks
Premise: This article assumes that you already know Decred and understand that it is a hybrid consensus mechanism between PoS and PoW, and understands the meaning of a double-flower attack (or 51% attack). Therefore, this article will not repeat them.
This article wants to answer the following questions:
- Jingdong has applied for nearly 200 blockchain patents, and the number of BAT blockchain patents ranks among the top 20 in the world.
- 66 times the income! Block.one is not afraid of huge amounts of money to buy back shares, is the SEC going to shoot?
- 10% layoffs, financing target fell to 150 million US dollars, the market is adjusting the framework after the market recovers
1. Is Decred's PoS and PoW hybrid consensus mechanism more resistant to double-flower attacks (often called 51% attacks) than Bitcoin's PoW consensus mechanism?
2. What is the result of a comparison in an equal competitive environment?
3. If the PoW and PoS hybrid consensus mechanism is more advantageous, how big is the advantage?
in conclusion:
1. At present, Decred's ability to resist double-flower attacks is not as good as Bitcoin. An effective double-strike attack on the Bitcoin blockchain will cost at least $1.6 billion in new hardware to succeed. The effective double-flower attack on Decred cost only $152.7 million in hardware and ballot (PoS) costs. Therefore, the cost of performing a Decred double-flower attack is only 9.5% of Bitcoin. For a currency whose current market value is only 0.23% of the market value of Bitcoin, it is not bad.
2. Therefore, in the competitive environment of the same market value, Decred's PoS and PoW hybrid mechanism is 41 times more resistant to double-flower attacks than Bitcoin's PoW mechanism…
Introduction
This article is mainly about a thought experiment in computer mathematics, trying to go deep into Decred. In the past year, Decred has made great progress. In May 2018, Decred's network computing power was 4,868 TH. Today, in May 2019, the network computing power was as high as 455,752 TH, an increase of 935% compared to last year. With the significant increase in computing power, the analytical data I released last year needs to be updated.
Last year's analysis compared Decred's ability to resist double-strike attacks with Bitcoin. At that time, Decred's PoS and PoW hybrid consensus mechanism was 11.24 times more powerful than Bitcoin's PoW. It is also conducted in an equal competitive environment, based on market value. But I can only compare the workload proof part of the consensus mechanism at the time of their respective hardware costs.
We later found that it was difficult to successfully perform a double-flower attack on Decred because the double-strike attack required the purchase of the votes required for the PoS consensus part of the Decred chain. Unless the attacker has a large number of votes, or has a quantum computer, it cannot be implemented.
In order to successfully perform a double-strike attack on the Decred chain, the attacker needs to master 51% of the network computing power, the same as Bitcoin. But unlike Bitcoin, Decred attackers need 60% of PoS mortgage funds to succeed!
Later, Decred leader Jake Yocom-Piatt added this:
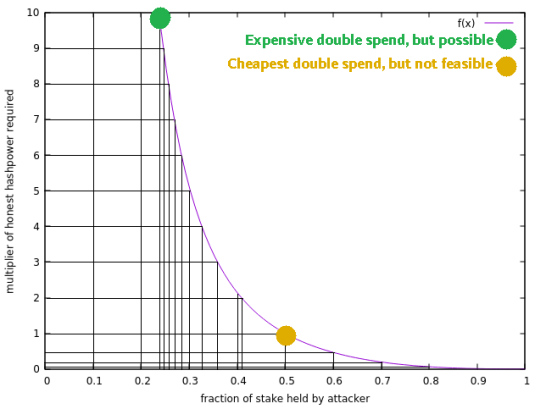
“Decred is highly resistant to typical double-flower attacks, such as the Finney attack, where the attacker conducts secret mining. Since the secret mining block needs to have more than 3 votes, for Secret, the secret mining It is more difficult. According to the technical part of Section 5.1 of the Proof-of-Activity paper, secret mining of Decred will require approximately 90% of computing power and 23% of mortgage funds. The curve shows the approximate percentage of PoW and PoS blending required for a double-flower attack, where the X-axis represents the partial mortgage required by the attacker and the y-axis represents the multiplier of the honest computing power required to be consistent with the honest chain."
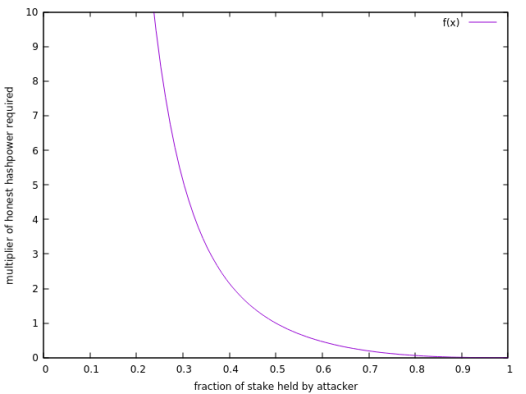
Based on the above information, it can be concluded that Decred's ability to resist double-flower attacks is 16.5 times that of Bitcoin when it is in an equal competitive environment. To update the data for this year and see if this number is still true. Don't forget that Decred's computing power has now risen 93.5 times…
First map the above chart to excel to see how the most effective double-flower attack on the Decred chain, how PoW and PoS need to be combined. The chart is updated as follows:
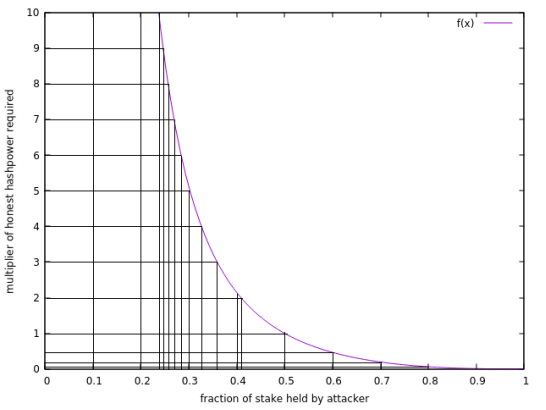
From the above chart we can conclude that in order to successfully perform a double-flower attack on Decred, there are the following solutions:
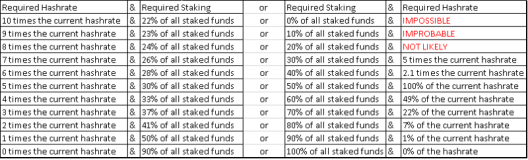
There are countless points on the purple curve, so there are countless programs. However, we only list the above 20 options.
Let's analyze some numbers first. At the time of writing (May 9, 2019), all Decrex's current token supply is 9,754,123. The current number of DCRs locked as a vote to verify the PoS portion of the Decred blockchain is 4,761,194, which is exactly 48.81% of the current total DCR supply. (Source: https://dcrstats.com/)
It’s crazy to lock the DCR for at least 30 days… This makes DCR extremely scarce compared to other cryptocurrencies. This also makes it very difficult to get a lot of DCR on the open market. Today, the entire DCR order book on most exchanges adds up to 43,410 DCRs, less than 0.5% of the total supply (0.45%)!
Therefore, if someone wants to perform a double-flower attack, there are only three ways:
A. Manufacture, install and operate Decred ASIC, long-term mining of Decred, and retain tokens or continually mortgage tokens.
B. Long-term purchase of a large number of DCRs and holdings, while trying not to raise prices in this way (considering the lack of DCR, this is very unlikely).
C. Crack the modern encryption technology with quantum computing and steal Decre's treasury key (but this can only steal about 610,200 DCRs, accounting for 6.26% of the total supply).
Mode C, although the most difficult, is probably the most effective (and most interesting) for successful double-strike attacks. The following is a thought experiment under situation C:
Stealing the Decred Treasury will cause the Decrex community to have low morale, which will cause prices to fall. Stakers will abandon the mortgage and sell DCR in the next few months, allowing attackers to buy more DCRs on the open market at a lower price. So, suppose the attacker gets 10% of the total DCR supply through this move. This will enable him to include about 20.5% of the mortgage funds, which is already very impressive. However, the attacker's computing power still needs to exceed 10 times the current computing power in order to carry out an effective double-flower attack (see the previous chart).
However, although the attacker can steal funds from the entire Decree treasury, he is still unable to perform a double-flower attack if his power is not more than 10 times the current computing power. This blockchain encryption system is also too complicated!
Therefore, Decred is hard to be attacked by double flowers. Let's go back to the cost calculation of the double flower attack. The chart below is an update of the previous chart that lists the cost of each scenario. However, for a variety of reasons, most situations cannot be implemented. But still show it to everyone.
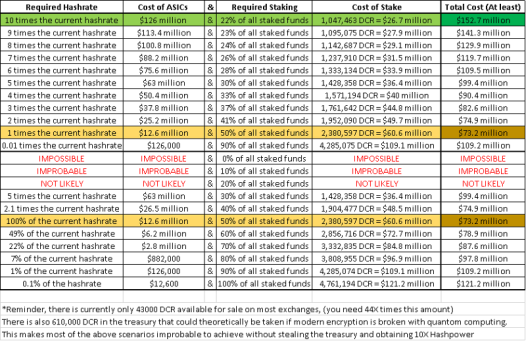
The above scheme can be calculated by the schemes listed previously. We found the proof of the workload by looking at the Decre ASIC hardware price and considering its power. Also consider the power factor. In addition, the cost of the PoS mortgage portion assumes that we can purchase as much Decred as possible at the current price on the open market.
Decred's 44TH mining power costs $900. The current computing power of the Decred network is 609.58 PETHASHES. Converting to TH is 609580TH/44TH = 13855 units. Since the double flower requires 10 times the computational power, multiply it by 10.
Therefore, I need to buy/manufacture/install/operate about 140,000 ASICs (and buy another 1% of the total DCR supply) to achieve the purple double-curve curve of the above chart. (Remember, quantum computer cracking modern encryption technology and stealing funds from the entire Decred treasury will not appear in the next 20 years).
So, what is the 140,000 ASIC multiplied by $900? Equal to $126 million… This is just the hardware price.
Each ASIC is 130 x 220 x 390mm, so it requires 651,652,303,305 square feet, or 60,540,480,000 square meters, or 14,959,879 acres of floor space to house these ASICs. So what is the concept of 15 million acres?
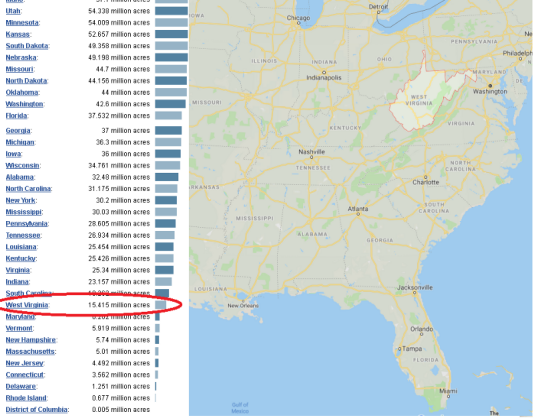
Almost equal to a West Virginia state, it has to be farmland, no roads.
So how much is an acre of farmland in West Virginia? The value of an acre is $2,570. We assume that the entire West Virginia state is farmland, so the acquisition of West Virginia requires 2,570 x 15 million acres = $38.55 billion. So many mines still need a lot of electricity, but there are several nuclear power plants in the area that can provide electricity (assuming we don't pay to steal a nuclear power plant).
How much power does it take to run 140,000 ASICs in West Virginia? Each miner needs 2,200 watts of power, so 2200 x 140000 ASIC = 308 megawatts (or 308 megawatts). The closest nuclear power plant to West Virginia is the Beaver Valley Nuclear Power Plant in Pennsylvania, which produces 1,835 megawatts of electricity! It’s more than enough to operate! (Assume that the transmission line can withstand the electrical load).
So suppose that we have now solved the modern encryption technology with quantum computers and then steal the Decreed treasury.
Then we buy 1% of the DCR supply for $2.5 million to get a 22% share of the mortgage. This will be able to perform a double flower attack on Decred!
In addition, the mortgage ballot pool needs to remain the same or decrease, and the Politeia governance mechanism needs to be offline, so the Decred community cannot change the consensus rules to prevent double-flower attacks.
Then we spent another $126 million to buy/manufacture 140,000 ASICs and have to build them in West Virginia.
So it took another $38.55 billion to acquire West Virginia land to house these mines.
We steal another Pennsylvania nuclear power plant to provide electricity (assuming these transmission lines can withstand 308 megawatts of electricity).
Then, the preparations for the double-flower attack on the Deccre blockchain were almost done, and it cost only $38.687 billion.
Wait. What is the market value of Decred?
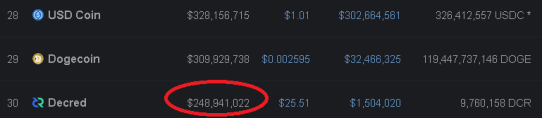
Let us ignore the cost of West Virginia, considering only the cost of ASICs and the cost of DCRs needed to purchase PoS votes on the open market. We also cannot use the quantum computers that do not exist to steal the treasury. We only assume that we bought the Decred treasury at the spot price of the market because "the community does not do things, Jake (Decred founder) is idle."
Therefore, the minimum total cost of performing a double-flower attack is $152.7 million. Equivalent to 61.3% of Decre's market value…
You may notice that this is the most expensive of the previous 20 scenarios (highlighted in green). And I chose this solution because it is the most feasible solution in reality.
The picture above shows that the most expensive solution is the most feasible
Let's compare the lowest cost solution (highlighted in gold). The cost of performing a double-flower attack on Decred is $73.2 million, which is equivalent to 29.4% of Decred's market value.
This golden scheme is unlikely to be achieved because no one can get 25% (minimum) of all DCRs in circulation, thus getting 50% of all mortgage tickets. Therefore, the scenario mentioned in the second section of this article refers to the first option (green scheme), which is to spend $152.7 million on the double-flower attack on Decred.
In order to compare Bitcoin with Decred, we need to know the conditions for performing a double-flower attack on Bitcoin. First, we need at least 51% of the bitcoin computing power. Bitcoin computing power is currently 50,641,334TH. There is a new and improved version of the Antminer t17 currently on sale, with a power of 40TH and a price of $1,268.
50,641,334TH/40TH = 1,266,033 units (this is the number of ASICs required to perform a 51% attack on the current Bitcoin network).
1268 x 1,266,033 ASIC = 1,605,330,287 USD
Therefore, the hardware cost of performing a double-strike attack on Bitcoin is $1,605,330,287.
The additional power required is: 1,266,033 ASIC x 2200 watts = 2,785,272,600 watts = 2,785 MW = 1 Pickering nuclear power plant.
The current market value of Bitcoin is $108 billion (as of May 9, 2019). So the cost of attacking the Bitcoin network ($1.6 billion) / ($10.8 billion) bitcoin market value = 1.5%.
Comparing the cost of Decred and Bitcoin to the market value, the ratio of Decred is 61.3%, and the ratio of Bitcoin is 1.5%…
So Decred: Bitcoin = 41 : 1
Therefore, we can conclude that Decred's ability to resist double flowers is 41 times stronger than Bitcoin in a competitive environment with equal market capitalization.
Wait, it seems that it is not right? In the second section of this article, I will explain why.
However, Decred's ability to resist double flowers is still very strong, even if it is not compared in an equal competitive environment. It can be said that it is stronger than the top ten currencies on CoinMarketCap.
in conclusion
All in all, this experiment is very interesting, demonstrating that Decred's PoW and PoS hybrid mechanisms are dual-safe, making it difficult to perform a double-strike attack on Decred, and may even be more resistant than Ethereum.
Although it is still relatively basic, I think this will become an increasingly important research area. In the second section of this article, I will explain to you why this analysis is completely useless and hopes to propose a better way to measure the double-flower resistance of different blockchains.
stay tuned.
Translator: Jill
Translation (original): First class warehouse https://first.vip/shareNews?id=1619&uid=1
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Institutional users are more likely to buy Bitcoin funds than Bitcoin?
- Does the Martin Act not apply to USDT? Bitfinex asks the judge to dismiss the lawsuit filed by the Attorney General of New York
- The 9th anniversary of the Bitcoin Pizza Festival, the story that the encrypted community has to say
- Babbitt column | Is there a bookmaker in Bitcoin?
- Senior code farmers are also recruited, BitGo engineer director stolen $100,000 bitcoin
- Blockchain
- Securities Pass 2.0 Agreement: Hybrid Securities Pass