Write the virus to the blockchain and never die? We did a bold experiment…
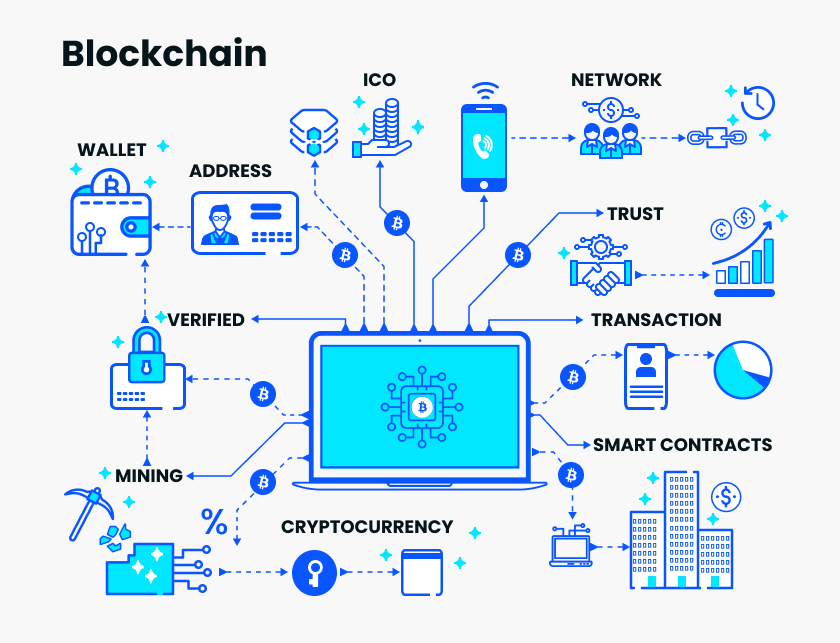
We all know that the data on the blockchain is not tamperable and permanently stored, so some people write their love for the blockchain, and some people write the property rights on the blockchain.
Imagine if you write malware on a blockchain, wouldn't thousands of miners become "seeders" for your malware?
Is it feasible to use blockchain to spread malware? What are the limitations of doing this?
- From atomic swapping to airdropping to forking, the SEC knows more about cryptocurrencies than you think.
- Party newspaper: the country's first blockchain membership card issued in Hangzhou
- BEPAL officially became a member of the Wanchain Galaxy Consensus Ecology, building a Wanwei Chain PoS node ecosystem
With these questions, Vaibhav Saini, co-founder of TowardsBlockchain and senior engineer in the blockchain, did a bold experiment. Let us go to his experiment to find out.
The following is his description of this experiment.
Since I joined the blockchain world in 2017, there has been a problem that has been bothering me:
The public chain such as Bitcoin is open to everyone. There are thousands of nodes in the blockchain network. They are all broadcasting messages to the network. From a hacker's point of view, this is a rare event. Seductive scene. So, technically, can we incite the entire blockchain network by infecting several nodes?
After several months of study and thinking, I mastered the working mechanism of the blockchain and got the answer to this question.
I have to say that this is a very interesting question, so I will condense my thinking process into this article, in which you will learn:
- Why is malware difficult to infect blockchain?
- Can we use blockchain, a decentralized system, to spread malware?
- A hands-on example of the spread of malware using the Decentralized File System IPFS and the Ethereum Storage Network Swarm.
Don't talk nonsense, let's get started! I believe this will be an interesting journey…
Why is malware difficult to infect blockchain?
In order to answer this question in detail, we will narrow down the discussion to the two public chains of Bitcoin and Ethereum.
As with all other blockchains, the nodes in the Bitcoin and Ethereum blockchains will communicate with other nodes and will enforce consensus rules to validate transactions and generate blocks.
Now let's consider the scenario of the attack. In order to spread the malware on the blockchain and eventually infect the blockchain, we need to do this:
- Step 1 : Send malware in the transaction.
- Step 2 : Take advantage of vulnerabilities in the Bitcoin client software.
It seems that these two steps are not difficult, but when you actually implement it, you will find that they have more or less problems.
For example, the problem with step 1 is that the amount of data we can send in a transaction is very small.
In the case of Bitcoin, the maximum capacity of the Bitcoin block is only 1MB. On average, the space occupied by each transaction is small, about 80 bytes.
Similarly, for Ethereum, the block gasLimit limits the size of the block and the complexity of the code. In other words, Ethereum also has restrictions on the size of the transaction.
Or it can be said that all blockchains are like this.
The problem with step 2 is that even if we send the code for the malware, it is a big problem to make the code work .
This is because:
- Transactions usually have a fixed format. Many blockchain clients will not receive messages that do not match the format.
- In fact, the execution environment of the code (such as the Ethereum virtual machine) has many restrictions, it only allows to execute several types of instructions. In addition, although Ethereum supports smart contracts and has a well-known Turing-complete programming language Solidity , the limitations of the Ethereum virtual machine (such as the very limited Ethereum instruction set and the very limited block fuel limit) allow the code to run in an environment. It is almost invisible with Turing.
And the code runtime environment of most blockchain systems is like this.
In addition, because client-side code is often open source, it is usually reviewed by a very large developer community before landing, which makes it impossible for us to find bugs in it.
Of course, I am not saying that these clients do not have loopholes. They just say that if there are loopholes, those hackers who rely on loopholes are used to execute the attacks, and there are few opportunities for us to miss them .
Can wicked people use blockchain to spread malware?
It's hard to use malware to infect the blockchain, but it doesn't stop us from experimenting. We are second to none, is it only feasible to use a blockchain to spread malware?
Although it is difficult to infect the blockchain system, the blockchain is fully capable of spreading the malware payload (code and files).
You may be wondering, we just said that due to the size of the transaction, it is almost impossible to package malware in a single transaction. This is the case, but who said that we can only use one transaction to spread malware?
Next we will use K-ary (K-ary) malware to do an experiment.
In fact, K-Malware is not new. If you have had some understanding of malware before, I believe that you will not be unfamiliar with it (anti-virus experts will say that you do not follow the routine).
K-Malware has infected many systems since its inception in 2007. In April last year, Lebanese scholar Joanna Moubarak published a paper detailing how to use the blockchain to spread K-Malware. I will then introduce this approach with a rigorous but interesting expression.
Unlike traditional malware that can only be loaded into one entity, K-ary malware can split the payload into K parts . Each of these parts looks like a normal executable and does not generate any indication of compromise (IOC, computer security terminology).
In principle, we have two ways to divide K parts:
- The K parts work in order . In this case, there is no need to ensure that the K parts of the malware are available at the same time and are activated at the same time;
- K parts work in parallel (working at the same time). In this case, the K parts of the malware must be available and activated during the same time period.
Of course, the specific division depends on the environment and system in which we are going to execute the attack.
In order to make the attack more concealed, we can also encrypt each part. In this case, however, we need to separately transfer the encrypted payload and the key used to decrypt the payload.
In addition, how do you ensure that the various parts of the malware are not out of the chain? Before execution, we can use the hash of the payload to verify that each part has joined the network.
You may ask, what is it for doing this? What can the blockchain help with the spread of K-Malware?
Using blockchain has the following advantages:
- The data on the blockchain is not modifiable, and the blockchain is not controlled by any single entity. This means that if we add malware to the blockchain, it is difficult for others to remove it from the blockchain.
- The use of cryptographic hash functions allows malware to easily verify the integrity of components. Since the data on the blockchain uses hash values (content-based addressing) instead of storage locations (location-based addressing) for indexing, this mechanism for protecting transactions from tampering can also be used to protect individual malware. Part of it has not been tampered with.
Demo: Using IPFS and Ethereum Storage Network Swarm to Spread Malware
Blockchain can spread malware, but how do you do this? Next we will demonstrate on the interstellar file system.
The malware here uses the Keylogger. First we scan it with anti-virus software. Then we will use the Star File System and the Ethereum Storage Network Swarm to store the malware payload and verify that the anti-virus software can find each. The part of the cat is greasy.
We first download a keylogger, I have already transferred it to the network disk, you can log in to the network disk to download. Next, we tried to scan with anti-virus software.
We can see that anti-virus software detects malware.
Now we divide the malware into K parts. Here we need to download and configure the interstellar file system first.
After the installation is complete, we use the following command to add malware to the interstellar file system.
Ipfs add <path-to-malware-file>
We will get this output.
At this point, our malware has been divided into K parts and stored in the interstellar file system. As shown in the figure above, the hash of this malware is:
QmNuAxMT9pepjZ26yXEk4T8qXofJrHoe7SxpoHa5WJ3T5x
If you want to view these K parts, we can use the following command:
Ipfs ls QmNuAxMT9pepjZ26yXEk4T8qXofJrHoe7SxpoHa5WJ3T5x
The output of the command is as follows:
The previous data is the hash value of each part of the file, we can use it to extract the corresponding part of the file.
Ipfs get <hash-of-chunk>
When we use a hash index to download a portion of a file, we can be completely sure that the file has not been tampered with.
After the download is complete, we will scan it with anti-virus software. At this point, the files in all parts of the malware can be verified.
The figure above shows that all parts of the malware are available, which means we can run a keylogger to steal information.
Note: The file is not permanently stored in the interstellar file system. Content that is not pinned in the system is deleted by the garbage collector (usually abbreviated as GC).
The Ethereum storage network Swarm provides a permanent storage service, and as such, it may be a better blockchain option. And Swarm works like the Star File System, where you can split the malware into K parts and then use its hash value as an index to download it.
*Disclaimer: The technology demonstrated in this article is only for technical exploration and knowledge. It is not recommended to try in any actual public chain. If you do this, you will be at your own risk.
Source | Hackernoon
Compilation | Guoxi
Editor | Aholiab
Produced | Blockchain Base Camp (blockchain_camp)
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Media: Don't let "Buffett lunch" become "Buffett curse"
- Gartner's latest forecast: 90% of corporate blockchain technology will be replaced in 2021
- Matrix Element was invited to attend the 2019 International Financial Technology Conference
- The tip of the iceberg: See how domestic listed companies "issue money" through Thunder
- DeFi solved a pain point and brought more pain points.
- BAT same PK blockchain: Ant's way, Baidu's device, Tencent's use
- Jimmy Song: Why is cryptocurrency decentralized investment meaning little?