Getting started with blockchain|What is SPV verification? It is enough to read this.
Source: Medium
Translation: First Class (First.VIP)
- In addition to Ping An’s account, what other companies that are “blockchain” will be listed?
- Research Report | Global Blockchain Investment and Financing Mapping
- Visiting Hong Kong Financial Technology Week, the head of Hong Kong's financial supervision looks at the blockchain like this
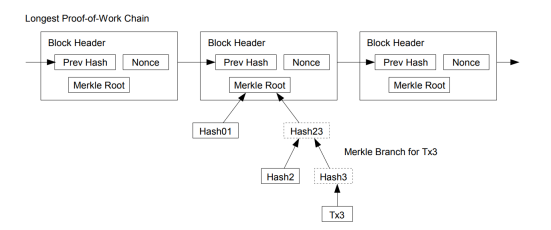
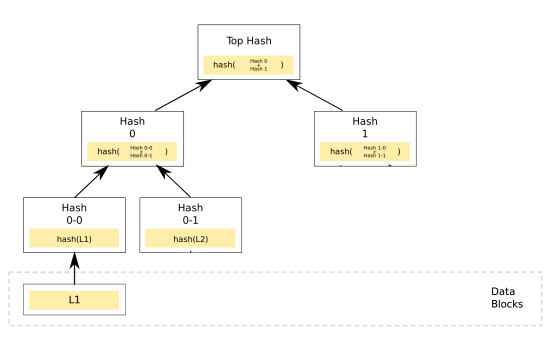
This is achievable because when Nakamoto designed bitcoin, he used a data structure called Merkel to store the transaction in each block. The Merkel tree is not a novelty. It is just a structure that groups all transactions in pairs and hashes them, then continues to hash the generated hashes until only the last one is left. Greek value (called Merkelgen). This constitutes a Merkel tree, where each node has two child nodes that can be used to create a parent node.
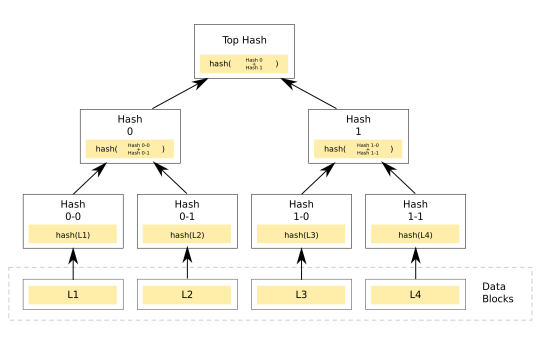
Above: Merkel tree view, L1~L4 is a bitcoin transaction
The cool thing about the Merkel tree is that only people who know Merkel/Top Hash can verify that the transaction is part of the tree. In other words, it is able to verify that the transaction is packaged in the Bitcoin area. In the block. It creates a proof by getting the nodes in the path connecting Merkelgen with one of the bottom transactions and bundling them together:
Above: Proof that SP1 has been included in the SPV certificate in the block
With this proof, only the original user who can access Merkelgen can trace the path back to the root in a verifiable way. He can verify that Hash1 and Hash0 are hashed to generate Merkel root, which means Hash1 and Hash0 is its legal child hash, and then the same validation is performed on Hash0-0 and Hash0-1 to prove that the two hashes are also part of the original block. Finally, check if L1 is the source of Hash0-0, proving that L1 has been packed into the block. If everything is correct, you can prove that this is an accepted bitcoin transaction.
Why is SPV proven so important?
Some people may say that the SPV certificate is not that great. After all, running a full node can verify bitcoin transactions. Why do you have to go around so many circles just to do the same thing? Be aware that running a full node requires downloading the entire blockchain, but if we use SPV proof, we only need to know the Merkel root of each block to verify the transaction, so each of our blocks only needs to store 80 words. Instead of storing the entire block like a full node. SPV proved to save over 99.99% of storage space, allowing us to verify in low-end devices or smart contracts, but if you want to download data for each block, low-end devices are completely impossible.
Disadvantages
If you successfully attack 51% of the cryptocurrency, the attacker can fool the client that relies on the SPV certificate to accept all invalid transactions, such as counterfeit currency transactions. If 51% of the attacks are successful, there may be double flowers, which breaks the basic security assumptions and causes harm to the entire system. However, in order to prevent this from happening, there are still many systems under study.
Please reprint the copyright information.
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Blockchain accelerates the scarcity of talents into the biggest challenge
- 4D long text | Bitcoin security model and declining block subsidies
- DeFi project party Compound completed $25 million in Series A financing, led by a16z
- Technical Interview | What is the dual offline payment for digital currency?
- General Trusteeship Research: Security Guardian of the Billion Pass
- Former Executive Director of PICC P&C Insurance: Innovation and Development of Insurance Blockchain
- The contemptuous currency circle is dying? Blockchain enters the era of ecological "card war"