Popular Science | Crypto War, Blockchain Technology
Source: Wanxiang Blockchain
On November 28, Gong Ming, a well-known entrepreneur and investor in the blockchain industry, as the lecturer of the fifth lesson, took dozens of important legends in the history of modern computer, cryptography & blockchain as Clues, from their stories, introduce the evolution of blockchain technology. Perhaps we are now accustomed to the changes and conveniences that the Internet brings to our lives, but have you ever thought that the development of technology has not occurred overnight? How many people's wisdom, exploration, dedication, and resistance brought humanity into the information from the industrial age? era. Similarly, blockchain technology does not fall from the sky. It is the crystallization of the wisdom of countless computer scientists, cryptographers, mathematicians, economists, and even philosophers. It is the thought and achievement of their unremitting exploration and dedication. From Turing to Satoshi Nakamoto, from the crypto-punk movement to the diversified development of technology, standing at a historical key point in the history of China's blockchain development in 2019, we have made significant contributions to these blockchain technologies. The story of the forerunners is more than a tribute. It also reminds us that the original intention of blockchain technology and the beliefs that a group of people have adhered to. Remind us of our predecessor's mission: to use the blockchain technology to really make this world better.

The following content is arranged according to the on-site shorthand, and some of the deletions do not affect the original intention:
- Is a cryptocurrency scam a new bottle of old wine? Tyler Winklevoss teaches you how to see through at a glance
- Why did Ethereum delay the "glacial period" three times? The new hard fork is coming again!
- QKL123 Blockchain List | Domestic media enthusiasm declines, some mining machines lose money (201911)
Prince Gong Ming
Hello everyone! My name is Gong Ming, and my net name is "Prince Gong". Today I want to analyze how the blockchain has developed to this today through some typical characters and stories in the development of the blockchain.
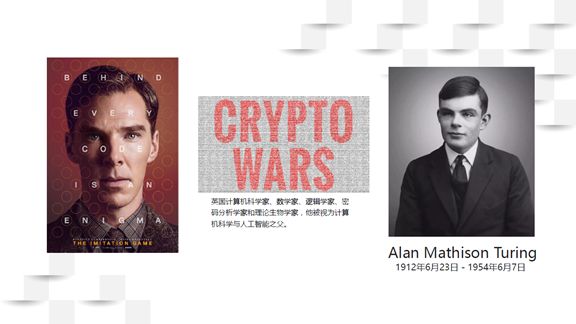
Let's start with a familiar character: Alan Masthison Turing. If you have watched "Imitation Game", you should know him. Turing is not only a mathematician, but also regarded as the father of computer science and artificial intelligence. But for a long time, his deeds have been buried, and gradually exposed after World War II.
Turing has many contributions, the biggest of which is in cryptography. He used machines against machines in a very interesting way during World War II. This idea is simple now, but it was shocking at the time. Turing ended the Second World War early by cracking the German password. Some people believe that Turing ended World War II at least two years in advance, and millions of people were rescued as a result. He made everyone aware of the important value of cryptography to the world, and its importance can even be said to be "nuclear bomb level".
Turing has many stories. He was persecuted by the British government after the end of World War II, and eventually led to suicide. There are also some conspiracy theories that call him homicide. Everyone knows that Turing died of eating apples dipped in potassium cyanide. Many people think of Apple's logo: a bite of an apple is in memory of Turing. But this is a rumor, just a beautiful coincidence. Apple did not consider this when designing the logo.
Turing's contribution has caused governments around the world to pay attention to the development of cryptography, but it has also caused some problems. That is, the government's strict control over cryptographic tools. Many people hope that cryptography tools should not only be in the hands of the government, and tools for cracking passwords are also developing rapidly. CRYPTO WARS (Crypto Wars) triggered this, so we have the next story.

Ralph C. Merkle is one of the inventors of asymmetric encryption. Earlier he was a member of the Xerox PARC laboratory, which invented the mouse, GU, IPU, Ethernet, ultra-large-scale robot circuits, OOP, and so on. There is a legend that when Jobs and Bill Gates visited the PARC laboratory, they saw the graphical interface provided by the laboratory, and then Bill Gates launched Windows, and Jobs founded NeXT.
In the history of computer technology, it was Merkle who first proposed the concept of asymmetric hashing. Hash algorithm is the most commonly used algorithm in the blockchain. Hash can turn any arbitrary field into a short string through a series of algorithms. The original text or code, even if it only changes one byte, The strings calculated by Greek are completely different, so they are commonly called "data fingerprints". The most common use case of the hash algorithm is that when you log in to the website, you need to enter your username and password. The system will convert the user password into a hash string and send it to the Internet. The other party ’s website can save your hash string. This way, even if the system is compromised, the username and password will not be leaked. This is a relatively common and simple application of hashing. Hash algorithms are used in almost all encryption protocols later.
Diffie and Hellman co-published the paper "The New Direction of Cryptography" in 1976, proposed the Diffie-Herman key exchange algorithm, and won the 2015 Turing Award. Diffie once said modestly that Merkle also put forward very important ideas in it, which he thought should be called the Diffie-Hellman-Merkle algorithm. They are not only the founders of modern cryptography, the founders of asymmetric cryptography, but also the enlightenment experts of modern currency and modern cryptography.

David Lee Chaum is a well-known cryptographic expert in the United States and a pioneer of cryptographic thought and movement. He has put forward a lot of interesting opinions on cryptography and privacy protection, has outstanding contributions, and has deeply affected many people. In 1983, he proposed the development of Ecash, an electronic currency based entirely on cryptography, and the earliest form of electronic money that proposed how to integrate cryptography into the currency system. In 1995, he founded DigiCash. He influenced many later cryptographic experts in the United States, most notably Tim May.
Tim May is also a pioneer in cryptography. He retired in his 30s at Intel because he achieved financial freedom with stocks. He spent a lot of time later on cryptography, exploring how to protect everyone's inherent right-"the right to privacy" through cryptographic tools.
John Gilmore shown in the picture above is also an expert in cryptography. If you have done network management or configured IP addresses, you will know that there is a protocol called DHCP-a standard protocol for automatically assigning IP addresses in a LAN. DHCP was written by John Gilmore of. Eric Hughes is also a very well-known cryptographer.
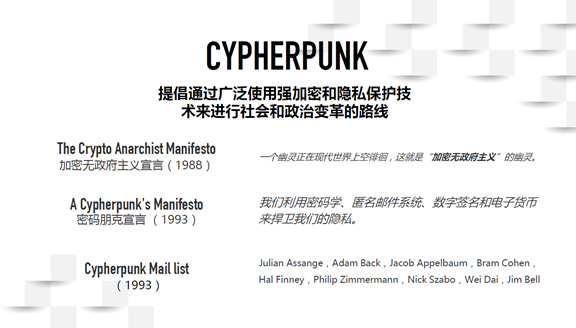
These experts were in the San Francisco Bay Area at the time, and often organized meetings to discuss cryptographic tools and future developments. They believe that cryptographic tools are very important and everyone should master them. They hope that through the tools, everyone can control their privacy again. Later, they proposed the concept of Cypherpunk.
It is said that the name was proposed by Jude Milhon. At the time, she was Eric Hughes's girlfriend and a famous female hacker. She also put forward many ideas on online feminism. Hacker originally refers to people with very good computer technology rather than people who attack the system. People who attack the network should actually be called crackers. After being translated into Chinese, it became a derogatory term because of the word "black". These people later changed their names to Geek. Cypherpunk advocates social and political change through the widespread use of strong encryption and privacy protection technologies. Cypherpunk is a political movement designed to put everyone's right to privacy back in their hands through cryptographic tools.
In 1988, Tim May wrote an article "Declaration of Crypto Anarchy", which for the first time proposed how to achieve some political demands through cryptographic tools. In 1993, Eric Hughes proposed the Crypto Punk Manifesto, which for the first time proposed that cryptography, anonymous mail systems, digital signatures, and electronic money would be used to defend human privacy. In 1993, the three of them formed the Cypherpunk Mail List email list. The so-called email list refers to the ability to communicate via email. They built new lists by constantly replying to emails, which was a more fashionable practice at the time, a bit like the BBS community behind. Since then, as new people have been added to the list, more and more people have participated in the discussion and actively contributed their own ideas, forming the Cypherpunk trend of thought.
Many people on this mailing list have since made a very important impact on the industry and the world, and even made important changes. For example, Julian Assange founded "WikiLeaks" in 2006, Adam Back proposed the new digital currency Hashcash, and later became the co-founder of Blockstream. Jacob Appelbaum is the founder of Tor Onion Network, and Bram Cohen founded BitTorrent. Hal Finney, Philip Zimmermann, Nick Szabo, and Wei Dai have promoted the development of blockchain technology.
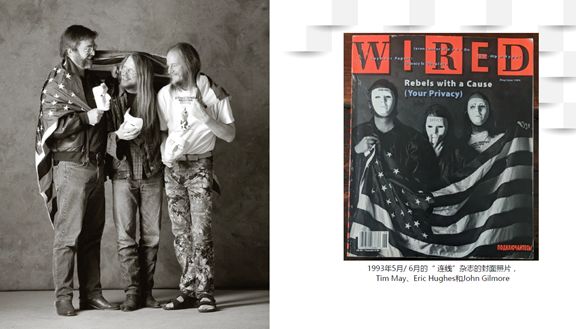
Tim May, Eric Hughes and John Gilmore pioneered the concept of Cypherpunk. The picture above is a photo of them. This photo, as the cover of Wired Magazine, has become a banner that has led many people to devote themselves to cryptography and made a great contribution.
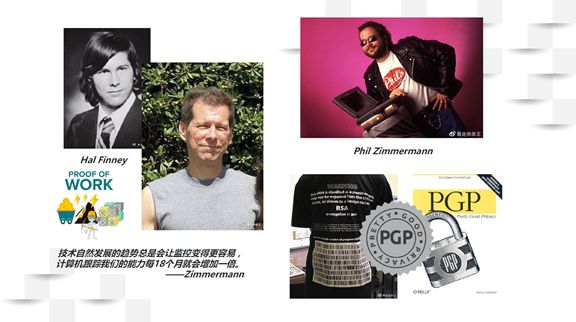
Hal Finney graduated from Caltech and is a very good cryptographer. Some people insist that Hal Finney may be Satoshi Nakamoto. The biggest reason is that he first wrote a reusable PoW (Proof of Work) mechanism. He was also the first employee of Phil Zimmermann and was deeply affected by it. Zimmermann was a pioneer in cryptography and his earliest contribution was to write PGP.
At that time, the Internet had no encryption protocol, which meant that all information was "streaking", and the US government could easily view anyone's information on the Internet. Zimmermann is both a cryptographer, a computer expert, and a social activist. He believes that this situation is not reasonable, and everyone has the right to protect their privacy. But the United States had the Cryptography Protection Act. This is why the first browser Netscape has two versions: the international version and the US version. The international version key is 40 bits, and the US version is 128 bits. Foreigners can only use 40 people. It is illegal to distribute 128-bit Nectscape to foreigners without permission.
Zimmermann wrote version PGP 1.0 in 1991, with 128-bit keys. The name of PGP is interesting-Pretty Good Privacy (a pretty good privacy tool). This tool shines a light on many people, especially individuals or organizations that do not want to be monitored by the US government. Zimmermann let everyone download PGP on the Ftp server, which aroused the alert of the US government. The FBI layer tried to sue Zimmermann and prevent him from spreading the tool.
Zimmermann believes that he has a responsibility to send "weapons" to everyone who needs them, so that everyone can use "weapons" to defend their privacy rights. So he co-authored a book with MIT, and published all the source code of PGP in the book. According to the First Amendment, Americans have freedom of speech, and freedom of expression includes freedom of publication, and books are not weapons. Zimmermann circumvented the then "Cryptography Protection Act" by publishing a book. The book has since been sold in large numbers around the world. Throughout, Zimmermann has resisted US government regulation through personal efforts and spread PGP to everyone around the world.

By 1993 and 1994, a large number of financial companies began to use high-level password encryption tools to protect their financial privacy, resulting in the complete failure of password control at that time. Eventually, the United States gradually deregulated and dropped allegations against Zimmermann.
As mentioned earlier, Hal Finney is the first employee of Zimmermann, and continues many of Zimmermann's work. He is also the main writer of PGP 2.0. Hal Finney met Satoshi Nakamoto early on the mailing list. In 2009, Hal Finney was diagnosed with gradual freezing disease. He continued to write code in a wheelchair with blinking eyes and small movements, and spent a long time writing a letter that told him how he knew Satoshi Nakamoto, how he was very lucky to participate in the Bitcoin network, Suggestions for the future direction of the Bitcoin network. In 2014, Hal Finney said goodbye to the world. He had previously contacted a specialized cryonics company and would freeze his body after his death, and maybe one day Hal Finney would be resurrected. Since Satoshi Nakamoto never appeared after Hal Finney was frozen, many people suspected that Satoshi Nakamoto was Hal.
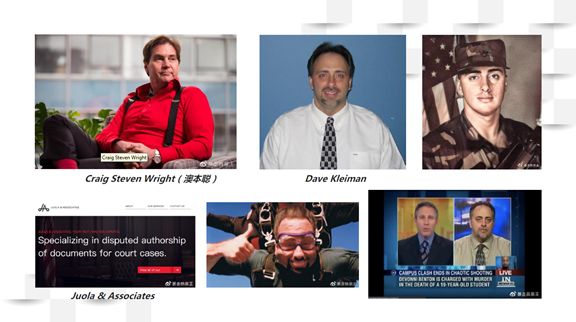
The discussion about who Satoshi Nakamoto is is continuing. Craig Steven Wright once said that he was Satoshi Nakamoto. Craig Steven Wright has deep knowledge in the fields of computer and cryptography and has done a lot of exploration. But Juola & Associates, a company that compared Craig Steven Wright's thesis and the Bitcoin white paper grammatically, concluded that the Bitcoin white paper was not 100% written by Craig Steven Wright. Craig Steven Wright also responded that the idea of Bitcoin is mine, but the white paper was written by his good friend Dave Kleiman. Dave Kleiman also entered the public eye for the first time.
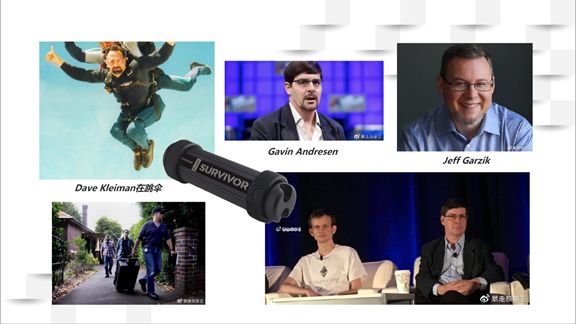
Who is Dave Kleiman? I have never heard of this person in the field of cryptography before. He is also an expert in cryptography. Born in Florida, USA, he joined the army very early. He served in Berlin and has loved computers since childhood. After leaving the army, he became a computer security forensic expert and worked as a computer security forensic officer at the Florida Police Department. He then entered a company and wrote "Immutable Security Audit Logging System." Is this name interesting? It seems similar to the immutable ledger system of Bitcoin and blockchain. As a security forensic expert, Dave Kleiman is also proficient in how to hide his tracks on the Internet. Unfortunately, he suffered a very serious car accident in 1996. Since then he has been paralyzed in a wheelchair and has a lot of time to spend on his computer.
After a lot of data verification, Dave Kleiman did cooperate with Craig Steven Wright computer company, and did mention Bitcoin. Does Nakamoto have a relationship with Dave Kleiman? This is a complex issue that is unknown.
For Dave Kleiman, we don't know much. His condition also deteriorated sharply after 2013. He was infected with super germs due to his prolonged bed staying and difficulty getting good care in the nursing home. All antibiotics have no way to kill superbugs, and treatment can only delay pain. Dave Kleiman lived in pain on the bed until his death, and was found dead in April 2013. The body was rotten when found. During the investigation, the police even found bullet holes in his bed and speculated that he probably tried suicide. It is unclear whether he succeeded or not. The main cause of death was due to a physical infection.
Nearly the time he died, Satoshi Nakamoto also disappeared. Will he be Satoshi Nakamoto? Everyone has their own opinions. Dave Kleiman left a very sturdy USB stick, currently in his brother's hands. Many people think that if he is Satoshi Nakamoto, the clue is likely to be in a USB flash drive. His best friend said that if you really think Dave Kleiman is Satoshi Nakamoto, then you give up. Because he knows that Dave Kleiman's password cannot be lower than 40 digits, and it is impossible to crack it by brute force.
Craig Steven Wright took out the legendary "Tulip Trust" and claimed that he entrusted Dave Kleiman with 1.1 million bitcoins in his care, and whether or not Dave Kleiman died, he would be returned to him at a certain time.
Many people think that Craig Steven Wright may be a liar, but it is very likely that he really knows Satoshi Nakamoto because he knows many details. Gavin Andresen has testified that Craig Steven Wright is really Satoshi Nakamoto. Gavin Andresen is considered a disciple of Satoshi Nakamoto, because Satoshi Nakamoto left a letter saying that everything was given to Gavin Andresen. Gavin Andresen is an American computer expert who does a lot of things. The algorithm is very powerful, and most of the bitcoin system code is currently completed under the leadership of Gavin Andresen.
Gavin Andresen is a very important person. Satoshi Nakamoto started, Gavin Andresen really brought Bitcoin to the world.
The second most important person on the Bitcoin network is Jeff Garzik. Jeff Garzik is also a very important developer, second only to Gavin Andresen, and has contributed more to the Bitcoin network code. Jeff Garzik was a Linux kernel developer before, and the code written by Jeff in Android is very powerful. Jeff Garzik said that when he first saw Bitcoin, he felt very interesting and important for the future. Jeff Garzik quit all his work and devoted himself to the construction of the Bitcoin community. He has stated that Craig Steven Wright is not Satoshi Nakamoto, and Kleiman is more likely.
"Who is Satoshi Nakamoto" is difficult to have a result in the short term, nor is it the topic of today. Whether it's Dave Kleiman, Gavin Andresen, or Hal Finney, they all contribute a lot to the Bitcoin network code. The blockchain has so far far surpassed the concept of Bitcoin and entered a whole new phase. However, the origin of the blockchain technology in the Bitcoin network is undoubted, and the world has gradually started to accept and believe in distributed ledgers.
When entering the Ethereum phase, a new vocabulary-Smart Contract (smart contract) appeared.
The inventor of the smart contract is Nick Szabo. He is not actually a computer expert, but a mathematician and philosopher. In 1993, he proposed smart contracts to explore whether computers and the Internet could be used to implement immutable contracts. Once this is done, many things can run completely automatically.
In 1993, smart contracts still existed like science fiction, and the advent of blockchain really made smart contracts possible. Now talking about the concept that the blockchain cannot leave smart contracts at all. Without smart contracts, blockchain will face great limitations in the future.
I often tell a joke that Satoshi Nakamoto is likely to be Chinese, and the name may mean "Chinese are inherently smart". Cryptography and blockchain technology have developed to this day, and it seems that no Chinese have been seen. But there is, Wei Dai.
Wei Dai is a very mysterious person and a great cryptographer. He studied cryptography early in the Microsoft research group. But until today, we don't know his exact identity. In 1993, he offered an idea B-money-anonymous distributed electronic cash. In addition to its name being similar to Bitcoin, B-money also mentioned all the elements that Bitcoin should have. Many people think that it is likely that Wei Dai inspired Satoshi Nakamoto, but Wei Dai said in an email that he thinks that Satoshi Nakamoto probably did not see B-money when he conceived Bitcoin, but completed it. After seeing the B-money paper, Satoshi Nakamoto's construction of Bitcoin should be completed independently. Many ideas of B-money are very close to Bitcoin. The first paper cited by Satoshi Bitcoin white paper is B-money. Bitcoin did not appear out of thin air, but was created on the basis of numerous attempts made by many people.
Vitalik Buterin puts smart contracts on the blockchain. Bitcoin is a peer-to-peer electronic cash system. Vitalik hopes to put all computers together to complete operations and become a supercomputer for smart contracts. Vitalik is a little genius, a Canadian of Russian descent. When I met him, he was only 19 years old. When he first arrived in China, he was a bit introverted and could not speak Chinese at all. He listened to us and turned the dictionary. I can speak Chinese in the second year, and can also send WeChat in Chinese. This brought us "fright", and perhaps geniuses look like this.
Gavin Wood is the CTO of Ethereum. Most of Ethereum's architecture is produced by Gavin Wood. He has written the Ethereum Technology Yellow Book, and many people rate his work extremely highly. Gavin Wood is leading Polkadot, mainly doing cross-chain.
I also adore Jed McCaleb. He is the founder of eDonkey. EMule is the earliest distributed download system. Jed McCaleb has participated in many well-known projects, and has used hash indexes for distributed systems since a long time, which has contributed greatly to the development of the industry.
So far the blockchain has developed to the point where the technology is very diverse. Not only the PoW proof-of-work mechanism, asymmetric encryption, and distributed systems mentioned above, such technologies as cross-chain, staking, zero-knowledge proof, sharding, side chain, and MPC have become more and more The more important. The future blockchain industry will be presented in a very diverse manner.
Everyone is discussing whether and when the blockchain can land. One of the key factors is that many technologies of the blockchain have not yet matured and are still in the process of rapid development.
In addition to blockchain technology, the definition of blockchain is also constantly changing. Now the blockchain is very different from the Bitcoin blockchain. At the time, the so-called blockchain was that information was linked together through a chain structure. Today, many technologies are no longer a chain structure, and have become a tree structure and a network structure. Technology like DAG is a meshed data structure.
Blockchain standards are also changing. Blockchain has unlimited possibilities in future development. Some people try to integrate all technologies into WEB3 to build the next generation Internet. It is the greatest thing to truly turn the so-called information Internet into the Internet of Value.
The current Internet is called the "Information Internet". The strongest part of the Internet is the transmission and replication of information, which is also the greatest value of the Internet at present. You send an email to a friend, and this email is still there when the other party receives the email. This is an endogenous function of the Internet-information transmission and replication.
How to transfer one dollar to your friend, and at the same time ensure that he adds exactly one dollar and you lose one dollar? The Internet can't do it, you must go through intermediaries, such as Alipay and banks. But this function is endogenous in WEB3, value transmission is the most basic function of the chain and does not need to be completed by an independent third party. This means that the transfer of value becomes an endogenous function, meaning that the transfer of value and the transfer of information are at the same speed. In the future, if value and information are at the same speed, the financial world will change dramatically.
At the WEB3 stage, you can really take everything into your hands, including privacy. Now all payment records, travel records, and taxi records are controlled by third-party intermediaries, and WEB3 has the ability to receive all data in its own hands, which is the direction of all future technology applications.
Blockchain is not conceived by one person's head. Many great people have made countless contributions, especially Hal Finney and Dave Kleiman. When Dave Kleiman and Hal Finney discussed Bitcoin, they probably did not know that the other party was in a wheelchair. These two wheelchair-bound cryptographers provided outstanding contributions to the development of digital currency and blockchain And they contributed all their wisdom and courage in the last moments of their lives. I personally think that the blockchain has been created by the smartest people in the world with all their efforts. In the 1990s, Cypherpunk raised the hope that by providing password tools, everyone will have their own privacy. Since then, many cryptographers have used their wisdom to promote the movement with all their strength. When we are talking about the usefulness of the blockchain, many people may not know, have forgotten, or have not heard of it at all. It turns out that the original intention is that blockchain is a cryptography that everyone can protect privacy. Tools, not just tools to make money. The unremitting efforts of these intelligent pioneers are to hope that blockchain technology can exert greater value in our hands.
Maybe these stories I shared today will be forgotten by everyone in an hour, but I hope that when you are anxious and embarrassed, think that many people are actually standing with us. Some people have given their lives, made a lot of contributions, and even gave their lives; when we talk about blockchain, we think of more than just hype. I believe this is just a stage in the crypto war. The great technology of blockchain will play a very big role in the future and have a huge impact on the world.
This is what I want to discuss with you today, thank you!
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Read Monero's Fair Mining Algorithm RandomX
- Seven years after its birth, the number of r / Bitcoin subscribers on Reddit exceeds 1.2 million
- Getting Started with Blockchain | What is DAO?
- Business of second-hand mining machines: business of acquaintances, pits of strangers
- Babbitt weekly selection 丨 Hainan hopes to become a national digital asset trading demonstration zone; Blockchain Service Network (BSN) settles in Hangzhou
- Increase the number of docking exchanges and switch to new blockchains, USDT market share still leads
- Featured | US Government Arrests Ethereum Developer Virgil Griffith; Billion Defi Market