The Internet of Things and the blockchain are a panoramic fusion. Wang Yongjuan, a strategic support force letter, talks about “blockchain + internet of things”
From October 12th to 13th, the "2019 CCF Blockchain Technology Conference" was officially opened in Chengdu. The conference was hosted by the China Computer Society and invited nearly 100 well-known experts from universities, industry, financial institutions, governments and domestic and international blockchains, including Chen Chun, academician of the Chinese Academy of Engineering, Zhou Zhongyi, academician of the Chinese Academy of Engineering, and financial technology. Expert Bai Shuo, Vice President and Chief Information Officer of the Bank of China, Ma Zhitao, Professor Zhang Yan of the University of Oslo, Norway, and Chairman of the Board of Directors of China Netan, and other distinguished guests, from universities, industry, financial institutions, government, and at home and abroad. Well-known experts in the field of blockchain jointly interpret the latest technological developments in the blockchain. Researcher Wang Yongjuan, a researcher at the School of Cyberspace Security, China Strategic Support Force Information Engineering University, attended the "Blockchain Technology and Network Security Sub-Forum" on the afternoon of the 12th and delivered a keynote speech on "Internet of Things Security Solutions Based on Blockchain Technology". She analyzes the past IoT security incidents and explains the application of blockchain in the field of Internet of Things. She believes that the blockchain and IoT scenarios are panoramic integration, and introduces some blockchain IoT real application scenarios.

The following is the content of the speech compiled by Babbitt (slightly deleted):
IoT security incident case:
- How to develop your own trading plan in the currency circle?
- Handwriting 丨 Joseph Lubin: The three major transformation directions of Ethereum and the moat
- To issue money and finance, you need to make a clear cut
1. On the eve of Christmas 2015 and 2016, the Ukrainian substation suffered two attacks. In the deep winter season, Ukraine, which is still colder than the ice city of Harbin, is in the snow and ice when it is preparing to celebrate Christmas. The attackers were from Russia. They implanted the malware framework virus Crash Override into the national grid, deployed it first, and then triggered the grid circuit through the 104 protocol, so that the power grid could be blackouted on a large scale.
2. The case of Jeep free light. In 2015, Uconnect, the version was 8.4An, used this attack to free light, you can replace the radio, turn on the wiper, and finally brake the engine. In addition to such an attack, with such a system, WIFI and cellular mobile attacks can also be performed, and the attacks are diversified and can be reproduced.
3. In addition to equipment and network attacks, more is the leakage of data traffic. In 2016, Marriott Hotel had a news leak of 500 million customers, and there was also a data leak in the state of China. This is a Facebook information leak. He also said that 50 million data is streaking and all stored in plaintext.
Analysis conclusions : The above several security incidents correspond to the various networks and equipment and the various crises that data will appear in the Internet of Things era.
Cause: First, the network device is unprotected. The cost of general equipment in the development of Internet of Things technology is subject to certain constraints. Cost, performance and efficiency are themselves impossible triangles.
Second, the security mechanism is not perfect, and different systems use different networks. In the Internet of Things, you use more networks, WIFI, Bluetooth, various narrow-band Internet of Things, various communication mechanisms, interactions between mechanisms, and parallel time of protocols. There are also many problems.
IoT security solution based on blockchain
If we want to know what blockchain technology can do for IoT security, we must first understand what kind of security threats IOT security faces, what security needs, and what needs to be done. This is the general architecture of the Internet of Things, usually divided into the sensing layer, the network layer, and the application layer .
The security problem of Internet technology itself has not been completely solved. With the vigorous development of the Internet of Things, in fact, the security problem is like spreading a cake. When the cake is getting bigger and bigger, the cake is getting thinner and thinner. This will happen in different architectures. Such a security issue.
Perception layer: The computing power, processing power and security of IoT devices are far from enough compared to the Internet era. It's easy for you to get your device, or to intercept your device, or to have the same batch of devices with you, because the protection functions are different, there are some node information stealing, service node attacks, these things are ubiquitous.
Network layer: I think the most important thing is cross-network attack. There are very few standards in the Internet of Things, standardization between communication protocols, and common technologies. In the network, information is falsified, forged, and so on.
Application layer: Application APP is first of all authorization and authentication issues, authentication issues are everywhere, illegal intrusion problems, information disclosure, remote eavesdropping and so on.
The key security requirements and corresponding problems to be solved in the Internet of Things era are first of all the issues of identity authentication and data protection. Secondly, network access requires a peer-to-peer network, and there are some technologies that require intrusion detection, access control, key management, and so on. This is a demand for the problem, I have to solve these problems.
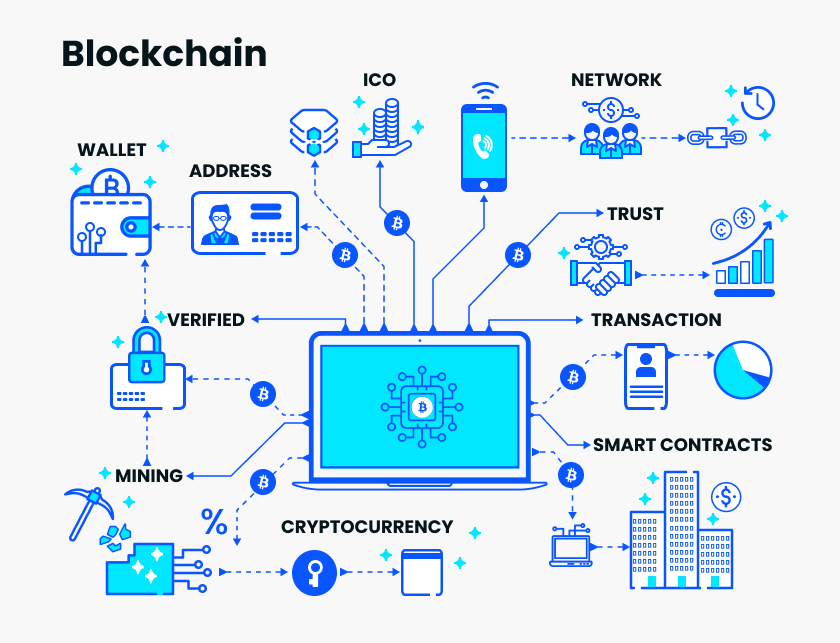
What kind of needs can the blockchain achieve?
The first is distributed network, peer-to-peer network environment, peer-to-peer network, distributed peer-to-peer, chain data block, anti-forgery and anti-tampering, authentication algorithm with signature, zero knowledge proof, attribute signature, and the same station. Advanced password technology such as encryption guarantees anti-counterfeiting and tamper resistance. Then there is the consensus mechanism to build a network of mutual trust and reliability.
For the Internet of Things, or for the network , the first thing that the blockchain does is to build trust . Even if I don't need to trust, I can also let the network run, and second, effectively reduce costs . Blockchain technology, especially cross-network financial services, works very well. There are also a lot of very good applications, and there are speeds to speed up transactions, which are reflected in the financial and supply chain.
The blockchain can solve the problems encountered in the Internet of Things from four aspects: information acquisition, data transmission, infrastructure and security privacy :
Information acquisition : Traceability can be traced through blockchain. Tracking traceability is a particularly useful scenario. There are a large number of distributed networks in the Internet of Things. This is a natural fusion scenario, and this traceability can ensure authenticity without further consideration. These, there is no problem with the center that can not trust the data.
Data transmission: It can connect different protocols and devices, and propose data capabilities in peer-to-peer networks such as management, query, and analysis.
Infrastructure layer: use the network peering and decentralization methods to calculate, store, network, etc., effectively open the link.
Security and privacy: This is the biggest feature of the blockchain as a data book. I personally think that in these aspects, it is possible to achieve security by loading.
Blockchain + IoT application case
I personally think that the blockchain and the Internet of Things itself are panoramic integration . I can use blockchain technology in the supply chain, such as logistics, supply chain finance, ports, etc., to realize information sharing in various departments and links. Information processing issues. Agricultural product traceability, agricultural credit and agricultural insurance, I would like to say that Henan University of Technology has a COFCO grain exchange, which applies blockchain technology to food traceability, which can effectively verify food production and price-related fluctuations. It is a very good try. Needless to say, medical big data, now IoT medical equipment is particularly large, everywhere, often at very cheap prices can buy heart rate, blood pressure, blood glucose equipment. These IoT devices have a connection to your digital healthcare system and can be used to ensure that data is not abused when you find health problems and related data problems. The abuse of data is actually very common in the medical industry.
I originally met a thing. Once I had a heart-and-cerebral vascular disease in my family, I gave him a drug. Later I checked the drug-related information online and may accidentally leave my phone online. Later, one month, every day, the medical supplier called me because I put the patient's symptoms, this is me accidentally, I shared the symptoms, then I thought, your condition is not yours. Privacy, second, do you see my information after I agree? If I apply the blockchain technology, I first implement data security, and the data is encrypted and stored. At the same time, you have to go through my authorization or partial authorization to implement the function grafting. This is in line with the most fundamental demands for data security. There are also environmental protection, intelligent manufacturing, new energy vehicle management, sharing economy, many of which are applicable to blockchain technology, and the smart rookie stations used now, etc., can have good application scenarios.
The application of blockchain technology in the Internet of Things is both horizontal and vertical.
Horizontal: It can open up the entire industrial chain of the Internet of Things. The entire information unequal in the industry can be solved through the blockchain. In the case of the consensus of the participants, data mining and partial utilization can be carried out, which can ensure data security and consistency, and at the same time open up the information barrier of the Internet of Things industry chain, for the Internet of Things. Improve high-quality data and increase the value of data utilization. I can connect IP devices to IoT devices to achieve data security and non-tampering. IoT collects data as the target object in the physical world. It is connected through the perceptual control domain. Virtualization is regarded as a digital asset. The data I generate is valuable. For me, it is an asset that I have produced myself. Through my target object, device, platform and other related identities, as well as data acquisition effectiveness. This can achieve a pair of assets, I think it offers a possibility.
If horizontal integration can achieve data collection and sharing of patients, hospitals, financial insurance, medical institutions, etc., many of them are now open in the horizontal direction. This is not a technical issue, it may be a problem of various barriers in various industries, so that a new blockchain + can be created. The Internet of Things security ecology.
Vertical: We can realize the credible, safe and efficient management of equipment identity and data through blockchain in the field of intelligent manufacturing, opening a new development channel for industrial IoT systems. Through the integration of vertical and horizontal integration, the integration channel of the IoT horizontal industry chain and the vertical industry chain will strengthen the consensus of the Internet of Things. In the Internet of Things era, you are a machine with various data, or a node in the Internet of Things.
The Challenge and Improvement of Blockchain + Internet of Things
The problem that exists now:
1. The problem of resource energy consumption . Blockchain technology itself is a high-performance technology. For example, bitcoin needs to be mined. This is very energy-intensive. The high energy consumption demand and the low processing power of IoT devices are very contradictory. This is a must. The reality. There is also the problem of data bloat, blockchain can only increase and can not be reduced, as the blockchain continues to increase, equipment is not enough storage space, I do not have such a large storage capacity and space, then what should I do? The blockchain is now 100G, but each IoT device node does not have large storage capacity. There is a performance platform. Blockchain technology is the most effective problem for it. The Ethereum now has some good ones. This morning, Academician Chen is also talking about the improvement of blockchain efficiency, and will become more and more in the future. Ok, but this problem still exists.
2. Partition tolerance issues . IoT equipment is very cheap, I need to be online all the way in implementing blockchain technology, but I don’t need to buy two things for IoT devices. I am very impressed with the change of the millet pedometer, because it is very cheap, it takes a while. No, this is the problem I have encountered. In response to these problems, some attempts or solutions are given from the perspective of blockchain and the Internet of Things.
Resource consumption, this is when I use the consensus mechanism, I do based on mining, based on credit and permissions, to do a high-energy application. The data is expanded, and the transaction record is compressed by the Merkel tree, and the data can be compressed by the structure. The performance bottleneck is not the data structure of the acyclic graph. The transaction mechanism is improved under the chain tolerance chain.
From the perspective of the Internet of Things, some solutions will be considered. With the transmission of low-energy WAN technology, transmission quality, distance and power consumption will also be solved, and data expansion problems will be given to Moore's Law, reducing storage costs and improving processing power. The performance bottleneck mainly depends on the promotion of chip technology.
You have to have a balance yourself, the equipment is more technical or more secure, you have the answer to know how to apply security technology, or blockchain technology should be applied. When blockchain technology is used for scene integration and communication, you have to have a vision. I am building a blockchain device or a blockchain community. These two questions are for you to understand, no matter what you do with IoT technology. Development or blockchain technology application, there will be an answer or direction in the heart.
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Emotion is the devil of investment, how to use the devil to earn money?
- China UnionPay Zhou Wei: Blockchain is infrastructure rather than tools, UnionPay will release heavy projects in the near future
- Behind Alipay and WeChat Joint "Sniper" Coin: Competition in cryptocurrency stocks
- "Gypsy" hoards bitcoin, holding more than 1,000 bitcoin addresses and growing at a record high
- [2019 CCF Blockchain Technology Conference] Topic: Focus on the frontier of blockchain technology, explore the application of industry
- Quote analysis: insufficient rebound power, the market has entered a downward trend
- A week of review | Libra received 5 "good guys card", and Telegram wants to receive a certificate