Introduction to Technology | Understanding Bulletproofs of Zero Knowledge Proof Algorithms –Range Proof III
Foreword
This article mainly shares the specific implementation details of the Bulletproofs-based Range proof, and makes a comparative analysis with the existing implementation on github.
Before reading this, I assume you have read:
Step1. Understand Bulletproofs-Range Proof I ( https://www.8btc.com/media/530155 )
Step2. Understanding the Bulletproofs of Zero Knowledge Proof Algorithm-Range Proof II ( https://www.8btc.com/media/532874 )
- Babbitt Column | Digital Economy and Digital Rule of Law
- Research report | Observation of the exploration of decentralized community governance from DAO, DCR to Polkadot
- About Token Classification Act, Libra, and SEC: Interview with Kristin Smith, Director of External Affairs, Blockchain Association
review
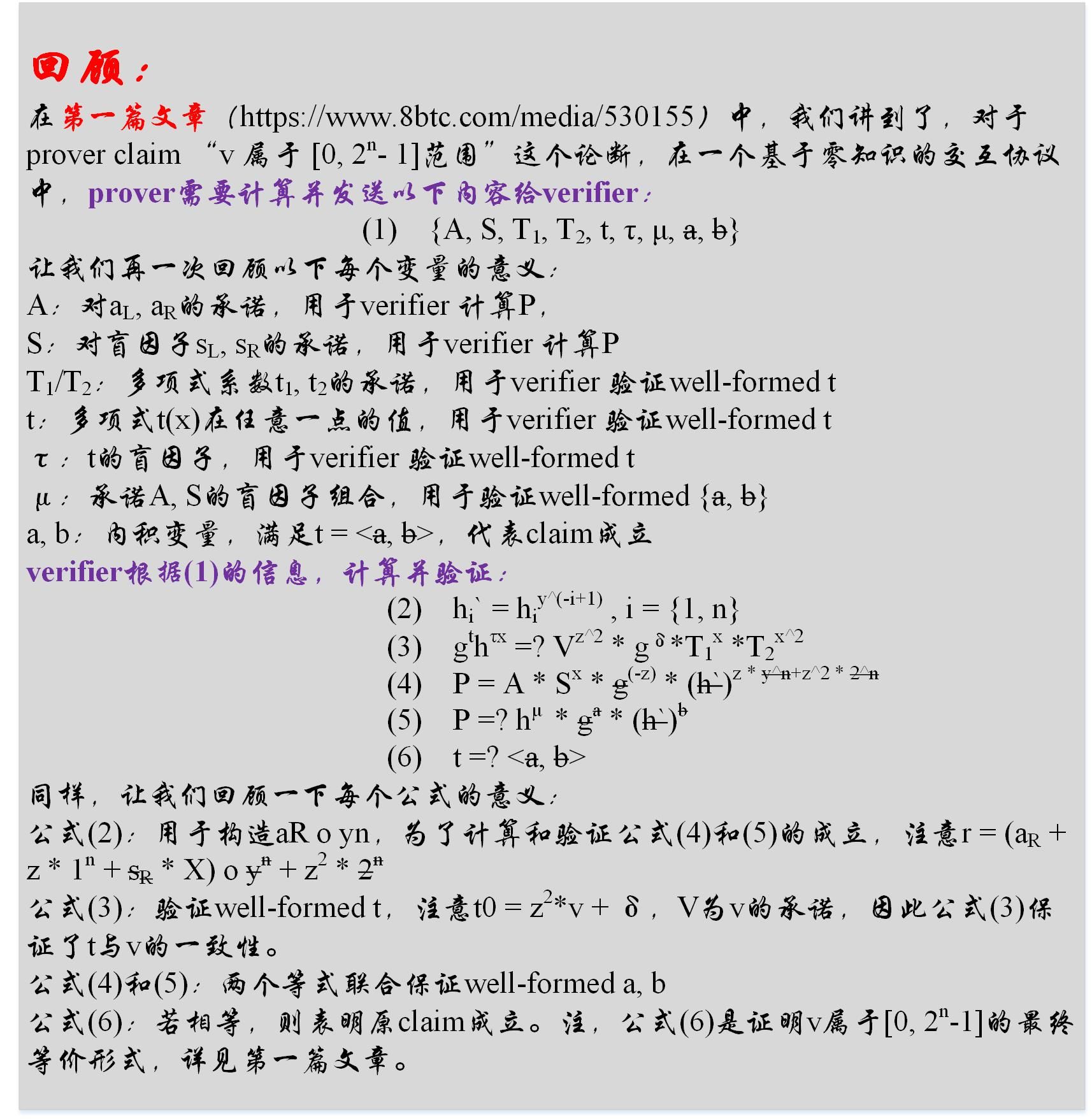
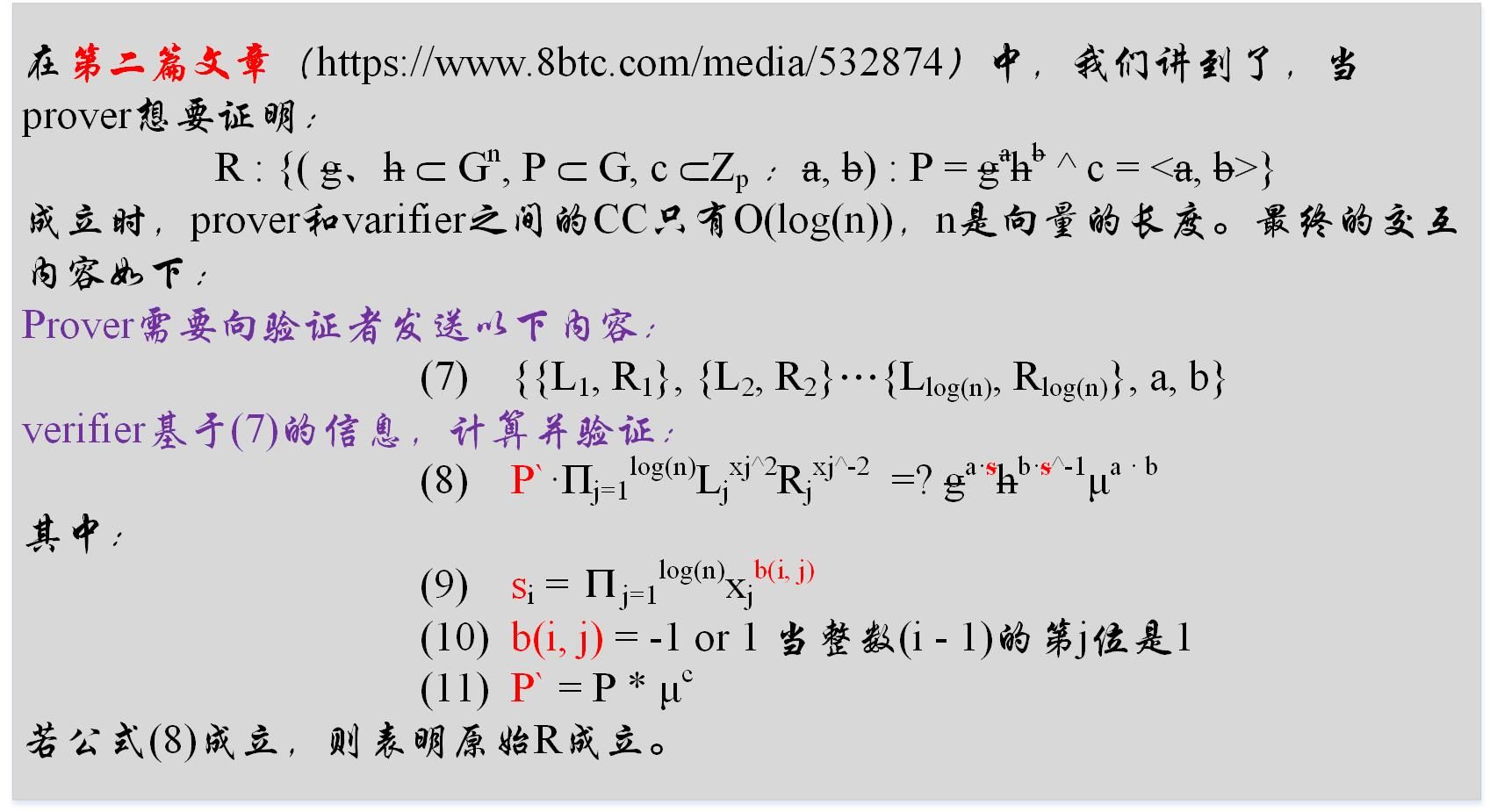
Range proof
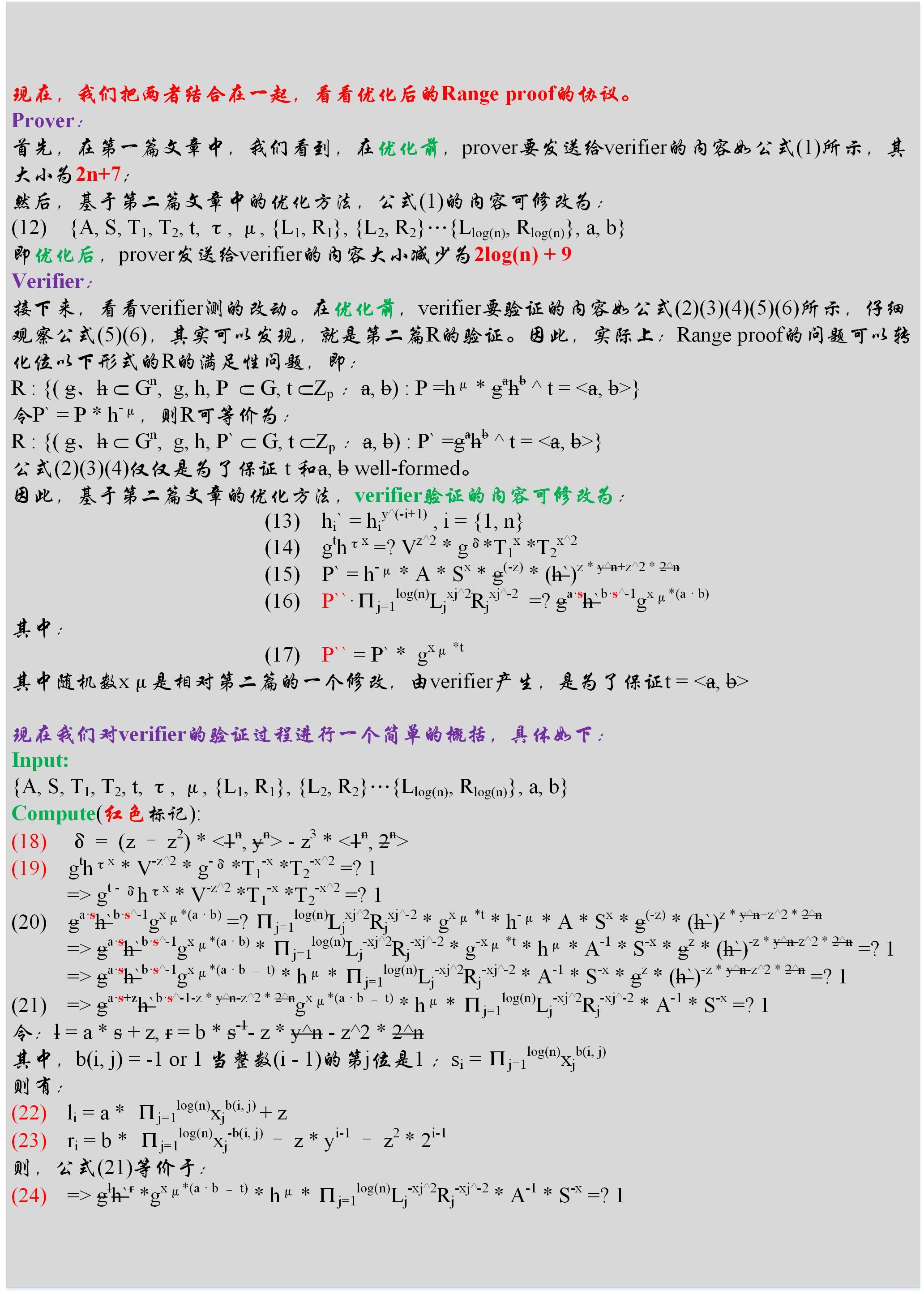
An open source implementation
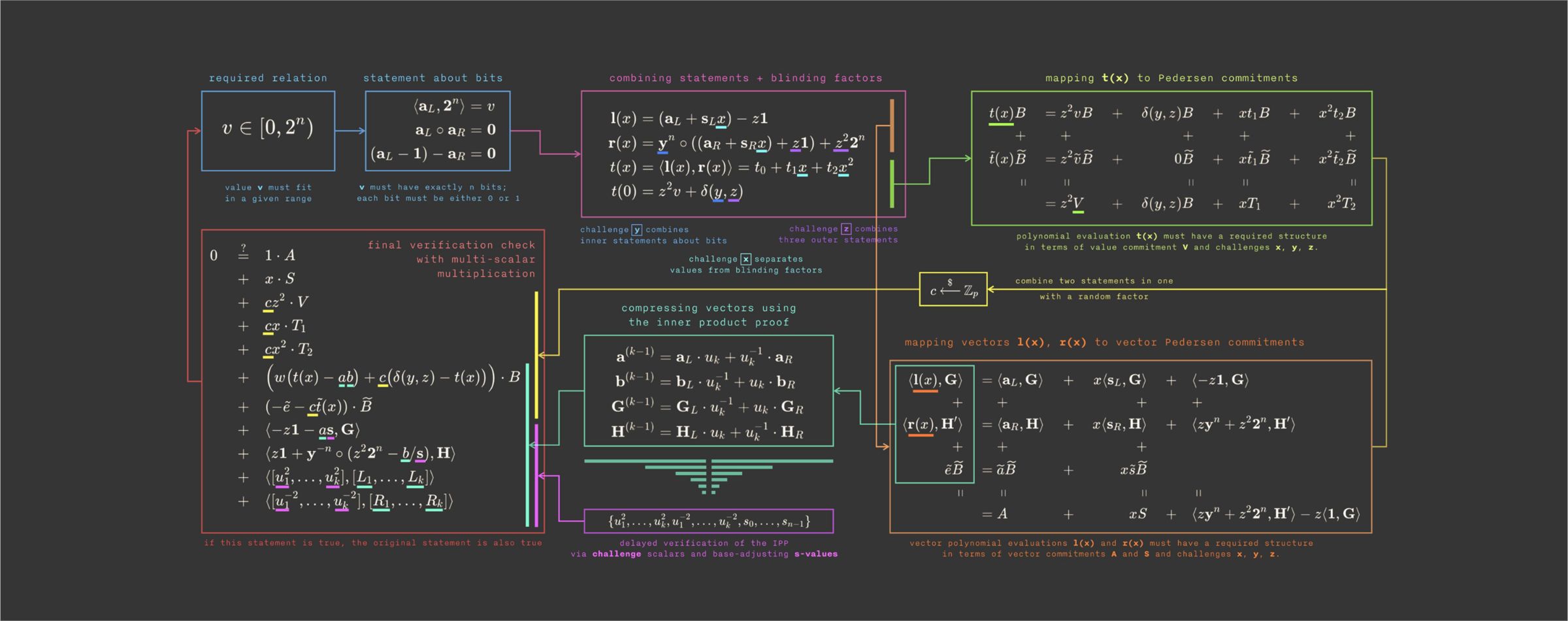
The open source implementation of Bulletproof's rangeproof. The project address is ( https://github.com/dalek-cryptography/bulletproofs ). Compared to the content shared in this article, the content shown in the following figure is mainly different from the following:
1. This article is based on the discrete logarithm; the figure is based on the discrete logarithm of the elliptic curve, so you only need to convert the exponential operation to the multiplication operation
2. The final verification content in the figure: it is actually a combination of formulas (19) and (24) in this article, using the assumption: if A c B = 1, then there is a high probability that A = 1 & B = 1. Therefore, equations (19) and (24) can be optimized into a verification equation, that is, (19) c (24) =? 1, if true, then equation (19) =? 1 & (24) =? 1 holds a high probability.
to sum up
This article mainly shares the implementation details of Range proof based on Bulletproofs. Combined with the previous two articles in this series, I believe that readers can have a relatively deep understanding of the principles behind Range proof. The next article will mainly share the application of Bulletproofs in general computing. thank you all
appendix
1. Bulletproofs paper: chrome-extension: //cdonnmffkdaoajfknoeeecmchibpmkmg/assets/pdf/web/viewer.html? File = https% 3A% 2F% 2Feprint.iacr.org% 2F2017% 2F1066.pdf
2. Bulletproofs project address: https://github.com/dalek-cryptography/bulletproofs
We will continue to update Blocking; if you have any questions or suggestions, please contact us!
Was this article helpful?
93 out of 132 found this helpful
Related articles
- Perspectives | MOV Ecology and Blockchain Thinking
- Babbitt Site | Super Ledger Beyond Fabric, 15 Projects in Progress, Reward 9 Cases
- Can't beat Bitcoin in 2019, where is the strength of Ethereum in 2020?
- ECB President makes clear statement on stablecoin: EU should lead the world in stablecoin projects
- Review Ethereum 2019: speak with data
- Industry Blockchain Weekly 丨 31 Provinces Release Policy Information, Blockchain Concept Stocks Expand
- Rebirth! Digital Assets (DA) receives $ 35 million Series C funding led by Australian Securities Exchange (ASX)